L12: Debates & Controversies
Why Controversy Matters: Moving Beyond Hype and FUD
01Every transformative technology arrives wrapped in competing narratives. Blockchain is no exception. Proponents describe an inevitable revolution in money, property rights, and organizational structure. Critics see a speculative mania propped up by technical complexity that obscures a lack of genuine utility. Both framings distort the truth, and both are commercially motivated. The engineer’s task is to cut through the noise with evidence and structured reasoning.
The stakes are high. Misallocated capital following blockchain hype cycles has destroyed billions of dollars of real-world wealth — the 2022 bear market erased over $2 trillion in market capitalization, and the collapse of the Terra/Luna stablecoin system alone wiped out approximately $40 billion in days. At the same time, excessive regulatory hostility based on incomplete understanding risks suppressing genuine financial innovation that could serve the unbanked and reduce friction in global commerce.
This lecture takes five contested questions head-on. First, does Bitcoin’s energy consumption constitute an unjustifiable environmental harm? Second, can regulators govern a protocol without a governing entity? Third, do central bank digital currencies co-opt or compete with blockchain’s promise? Fourth, does crypto concentrate wealth rather than distribute it? Fifth, what does an honest forecast of blockchain’s trajectory look like? Each question has defensible answers on multiple sides — which is precisely why your ability to reason through the evidence rather than defer to a tribe matters.
The Energy Debate: Environmental Cost of Consensus
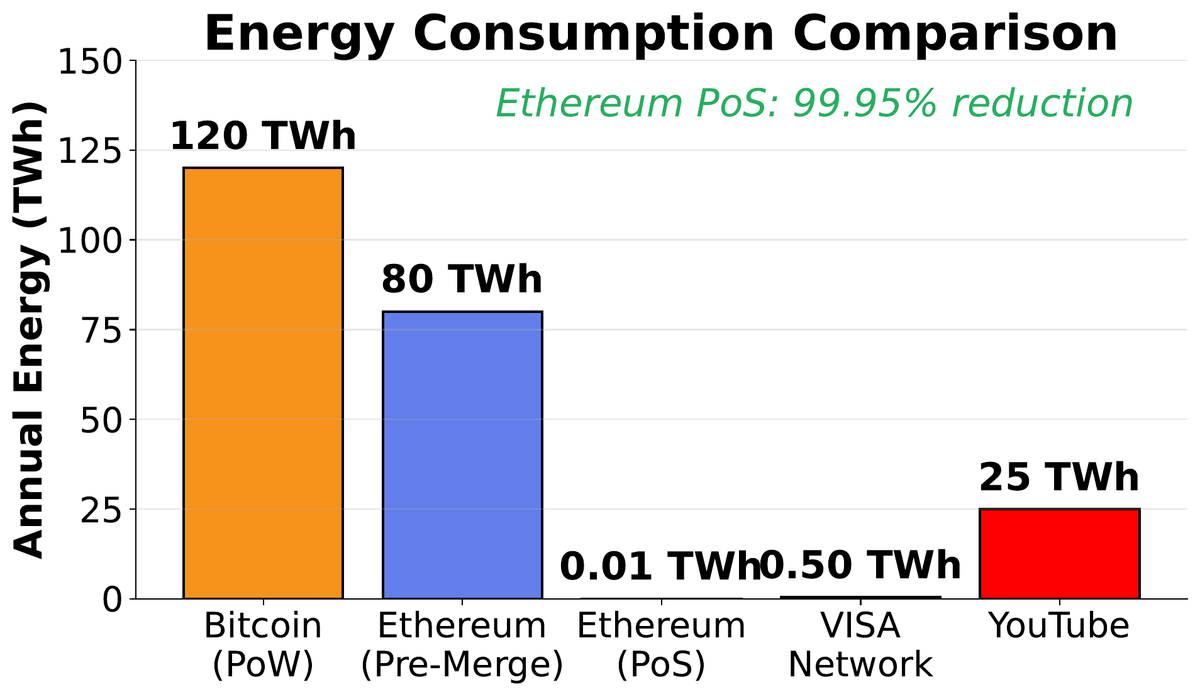
02Bitcoin’s Proof-of-Work consensus requires miners to perform vast quantities of purposeless computation — SHA-256 hashing repeated billions of times per second across millions of specialized machines worldwide. The Cambridge Centre for Alternative Finance estimates annualized Bitcoin electricity consumption in the range of 100–150 TWh, comparable to countries like Poland or Argentina. Critics argue that this energy expenditure produces no economic output beyond securing the ledger. Defenders counter that the energy is precisely the point: real-world cost is what prevents double-spending cheaply.
The debate hinges on three sub-questions that are frequently conflated. First, how much energy does Bitcoin actually consume, and what is the marginal cost of each transaction? Second, what fraction comes from renewable or stranded sources? Third, how does the comparison to alternative payment systems hold up under honest accounting?
The Critique
Bitcoin uses >100 TWh/year — electricity that could power tens of millions of homes. Each Bitcoin transaction consumes energy equivalent to hundreds of thousands of Visa transactions. The network’s difficulty adjustment ensures that energy use scales with Bitcoin price, not with transaction volume, meaning efficiency gains from better hardware are entirely offset by more mining.The Defence
Between 50–70% of Bitcoin mining uses renewable or stranded energy (methane flaring, curtailed hydro). The global banking system — branches, ATMs, data centres, security infrastructure — uses an estimated 250 TWh/year, with less transparency. Security requires cost by design. PoS may not provide equivalent Sybil resistance at the limit.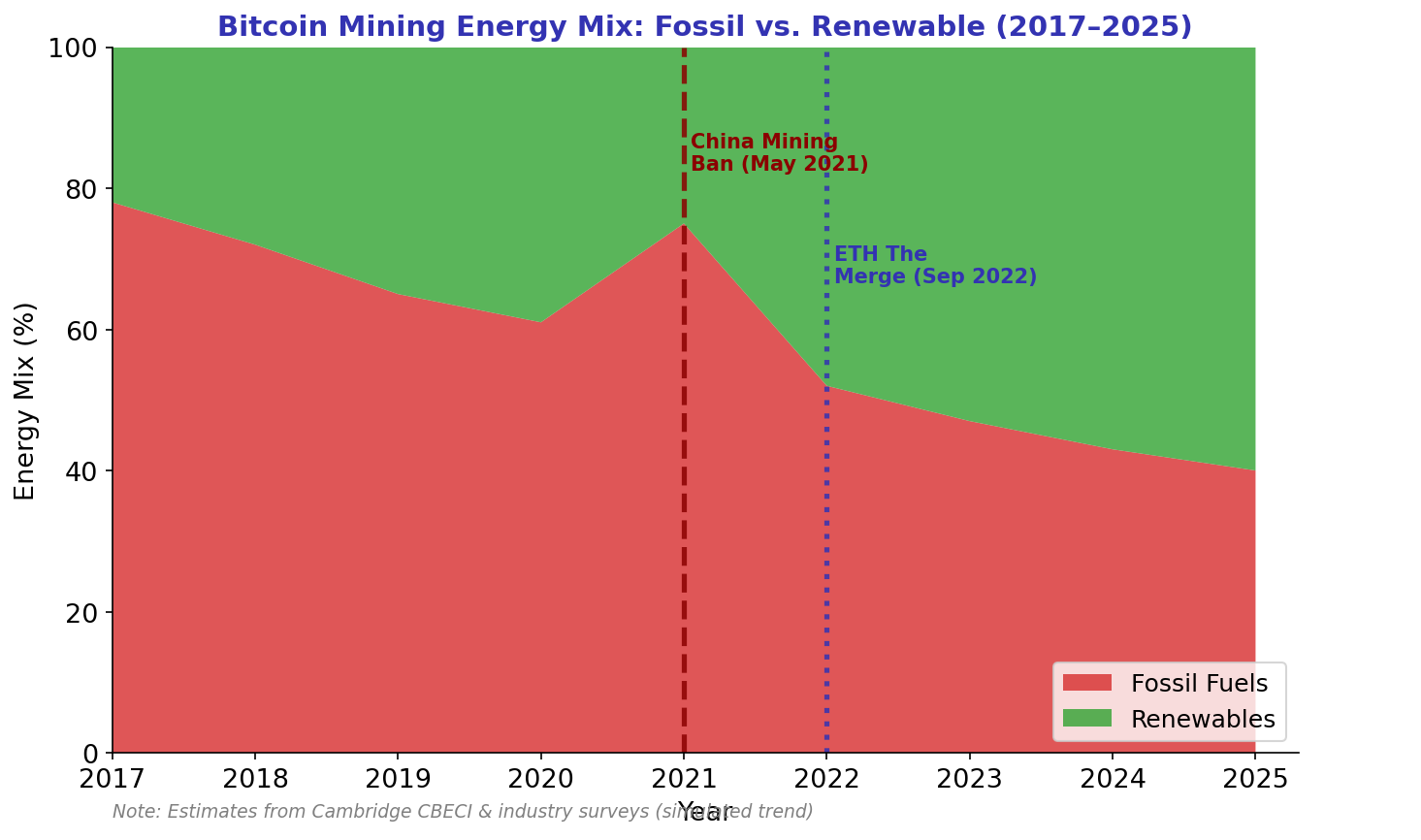
The intellectually honest position: PoW Bitcoin’s energy use is a genuine environmental externality that the Bitcoin community has chosen to accept as the price of trustless, permissionless, censorship-resistant value transfer. Whether that price is worth paying depends on one’s assessment of the value created. It is not a dismissible concern, nor is it unique to blockchain as a category of technology. The Ethereum transition to PoS demonstrates that alternative designs exist; Bitcoin’s community has made a conscious philosophical choice not to adopt them.
The Regulatory Landscape: Governing the Ungovernable
03Blockchain was explicitly designed to be censorship-resistant and jurisdiction-agnostic. Satoshi Nakamoto’s protocol has no headquarters, no CEO, no registered legal entity. This architectural property creates a fundamental challenge for regulators whose enforcement tools — court orders, asset freezes, license revocations, injunctions against legal persons — require addressable entities. How do you regulate a protocol?
The answer emerging across jurisdictions is: regulate the on-ramps and off-ramps. Exchanges, custodians, stablecoin issuers, and other entities that hold user funds or convert between crypto and fiat are legal entities in specific jurisdictions and can be licensed, regulated, and sanctioned. This approach captures a significant fraction of user activity while leaving the base layer protocol itself untouched.

| Jurisdiction | Approach | Key Framework | Crypto Status | DeFi Position |
|---|---|---|---|---|
| European Union | Comprehensive regulation | MiCA (2023) | Legal | Under review |
| United States | Enforcement-led | SEC / CFTC authority | Legal, contested | Hostile |
| United Kingdom | Risk-based licensing | FCA regime | Legal | Cautious |
| Singapore | Regulatory sandbox | MAS framework | Legal | Exploratory |
| UAE / Dubai | Pro-innovation | VARA / ADGM | Legal | Permitted |
| China | Complete prohibition | 2021 PBOC ban | Banned | Banned |
| El Salvador | Legal tender adoption | Bitcoin Law 2021 | Legal tender | Permitted |
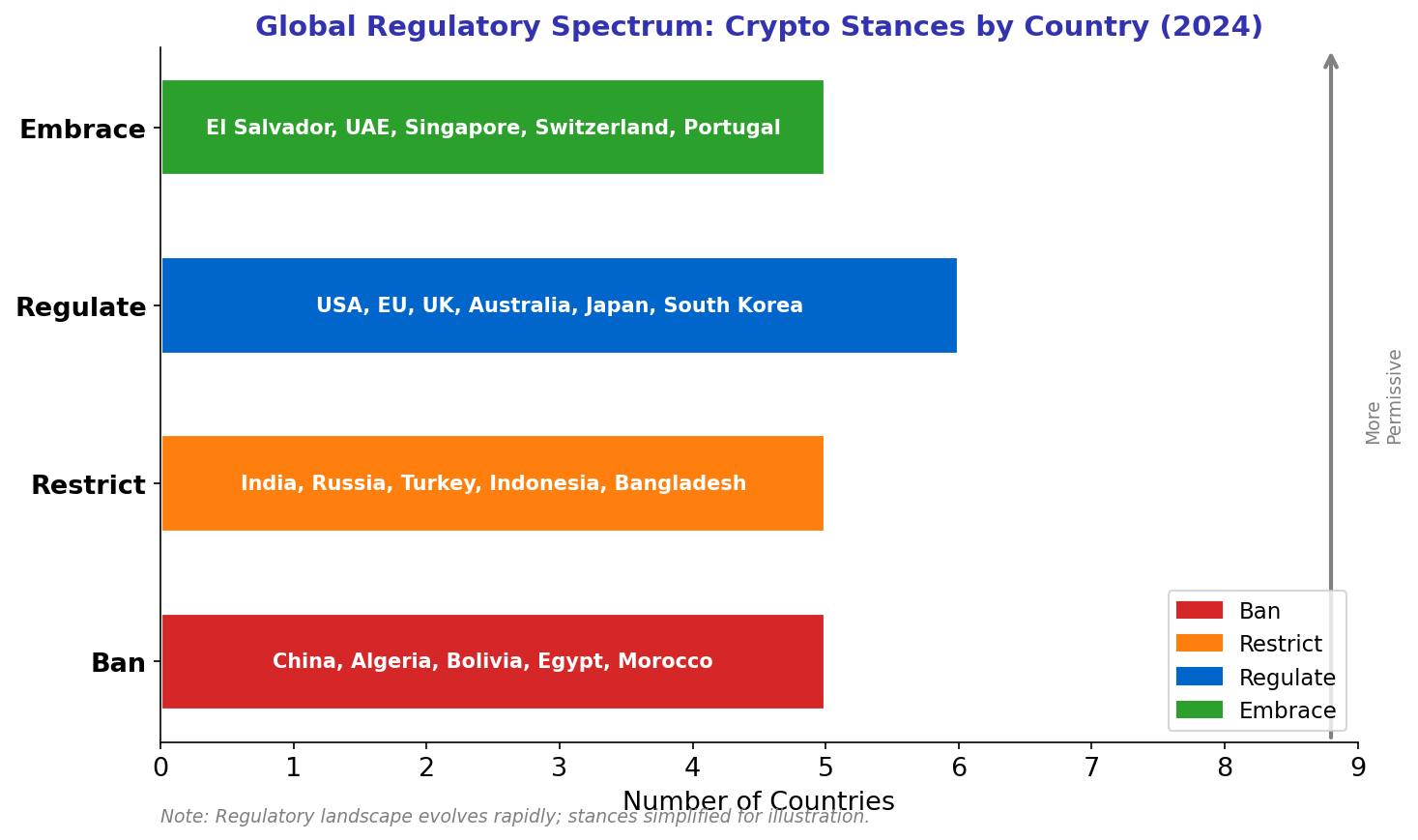
The EU’s Markets in Crypto-Assets (MiCA) regulation, fully effective in 2024, is the most comprehensive framework yet. It establishes licensing requirements for crypto-asset service providers, imposes reserve requirements and redemption rights for stablecoins, and sets disclosure obligations for token issuers. The regulation does not cover DeFi protocols directly — an intentional gap acknowledged by regulators who lack the tools to do so effectively. The DeFi frontier remains a live regulatory question in every jurisdiction.
CBDCs: Digital Money by Central Banks
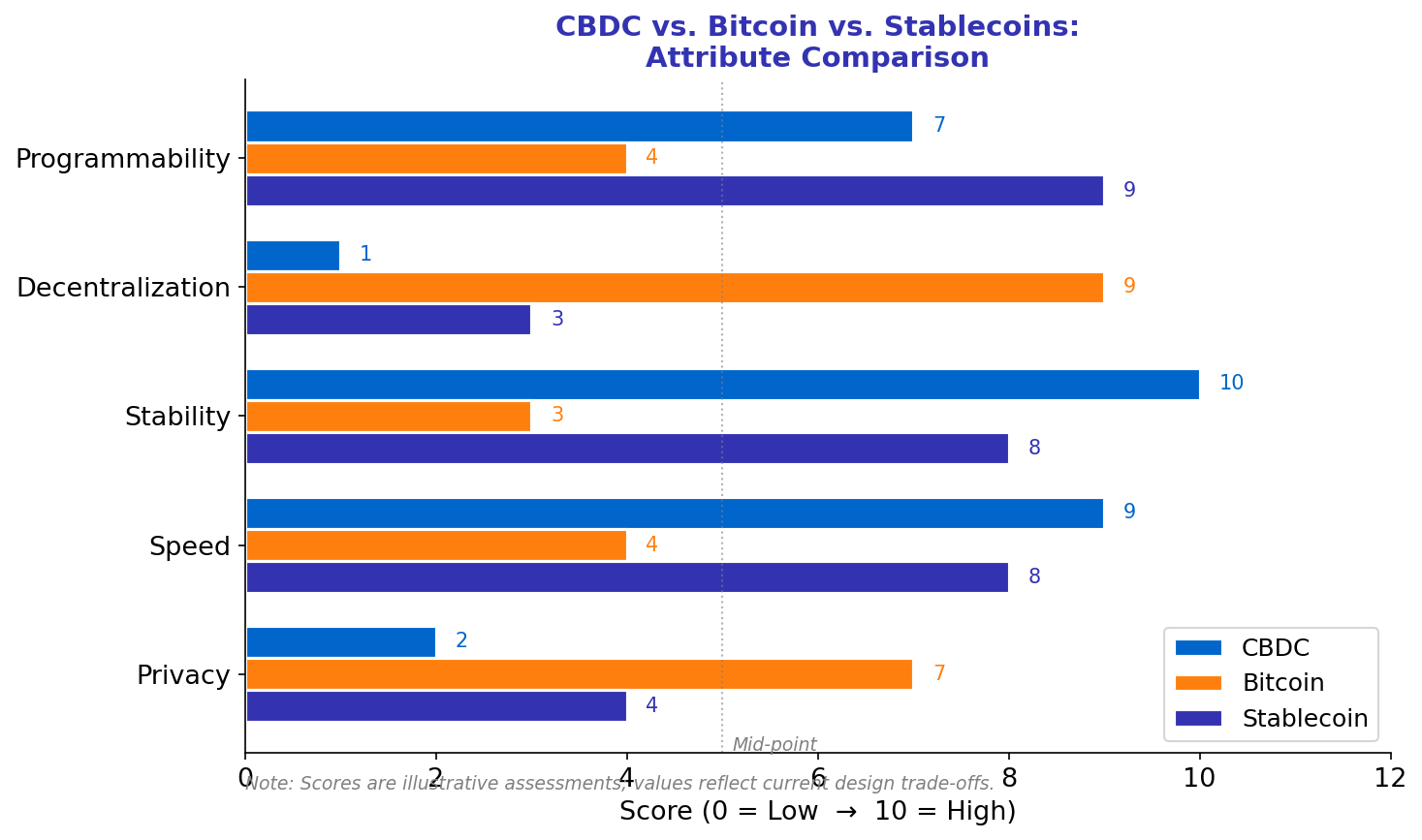
04The most significant institutional response to blockchain’s monetary challenge has been the rapid development of Central Bank Digital Currencies. As of 2024, over 130 countries representing more than 98% of global GDP are actively exploring, piloting, or deploying CBDCs. China’s digital yuan (e-CNY) has processed hundreds of millions of transactions. The Bahamas’ Sand Dollar, Jamaica’s JAM-DEX, and Nigeria’s eNaira are in live deployment. The European Central Bank has concluded its digital euro investigation phase and begun preparation.
CBDCs and decentralized cryptocurrencies share the digital form and often some blockchain-adjacent infrastructure, but they differ fundamentally in their governance philosophy. A CBDC is a direct liability of the central bank — the state’s most trusted financial institution. A CBDC transaction is reversible by the issuing authority. A CBDC wallet can be frozen, audited, or programmed with spending restrictions. These are features from a state perspective and bugs from a cypherpunk perspective.
| Dimension | Physical Cash | Commercial Bank Deposit | CBDC | Bitcoin / Crypto |
|---|---|---|---|---|
| Issuer | Central bank | Commercial bank | Central bank | Protocol / miners |
| Liability of | Central bank | Commercial bank | Central bank | No one (bearer asset) |
| Privacy | High | Low (KYC) | Low (tracked) | Pseudonymous |
| Programmable | No | Limited | Yes | Via smart contracts |
| Permissionless | Yes | No | No | Yes |
| Reversible | No | Yes (by bank) | Yes (by central bank) | No |
The competitive dynamic between CBDCs and decentralized crypto is less winner-takes-all than often portrayed. CBDCs are likely to displace some cryptocurrency use cases in jurisdictions with stable monetary policy and trusted governments, particularly for retail payments. But CBDCs cannot replicate the censorship-resistance, global accessibility, or permissionless programmability that drive crypto adoption in capital-controlled economies, among the unbanked, and in DeFi applications. The two may coexist as complements serving different needs rather than direct substitutes.
Adoption Reality: S-Curves, Barriers, and Institutions
05Technology adoption historically follows an S-shaped curve: slow initial uptake by innovators and early adopters, rapid acceleration as network effects compound and usability improves, then deceleration as the addressable market saturates. As of 2024, estimates place global crypto user counts at 600–800 million, concentrated in Asia, Latin America, and Sub-Saharan Africa. This is roughly the adoption level of internet users in the mid-1990s — significant but far from mainstream.
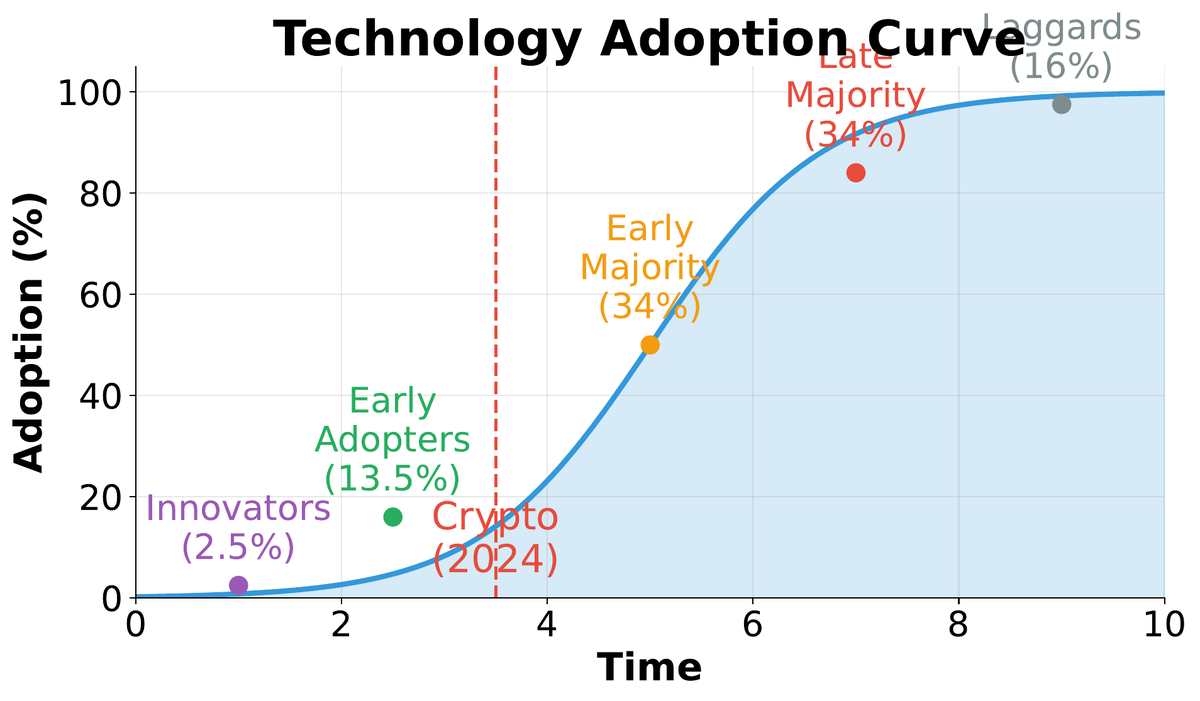
The approval of spot Bitcoin ETFs in the United States in January 2024 marked a structural shift in institutional access. For the first time, regulated investment vehicles with fiduciary obligations could hold Bitcoin exposure without managing private keys or interacting with crypto-native infrastructure. Blackrock’s iShares Bitcoin Trust attracted over $10 billion in assets within weeks of launch — the fastest ETF product launch in history. This signals a transition from the “early adopter” to the “early majority” phase of the adoption curve for Bitcoin specifically.
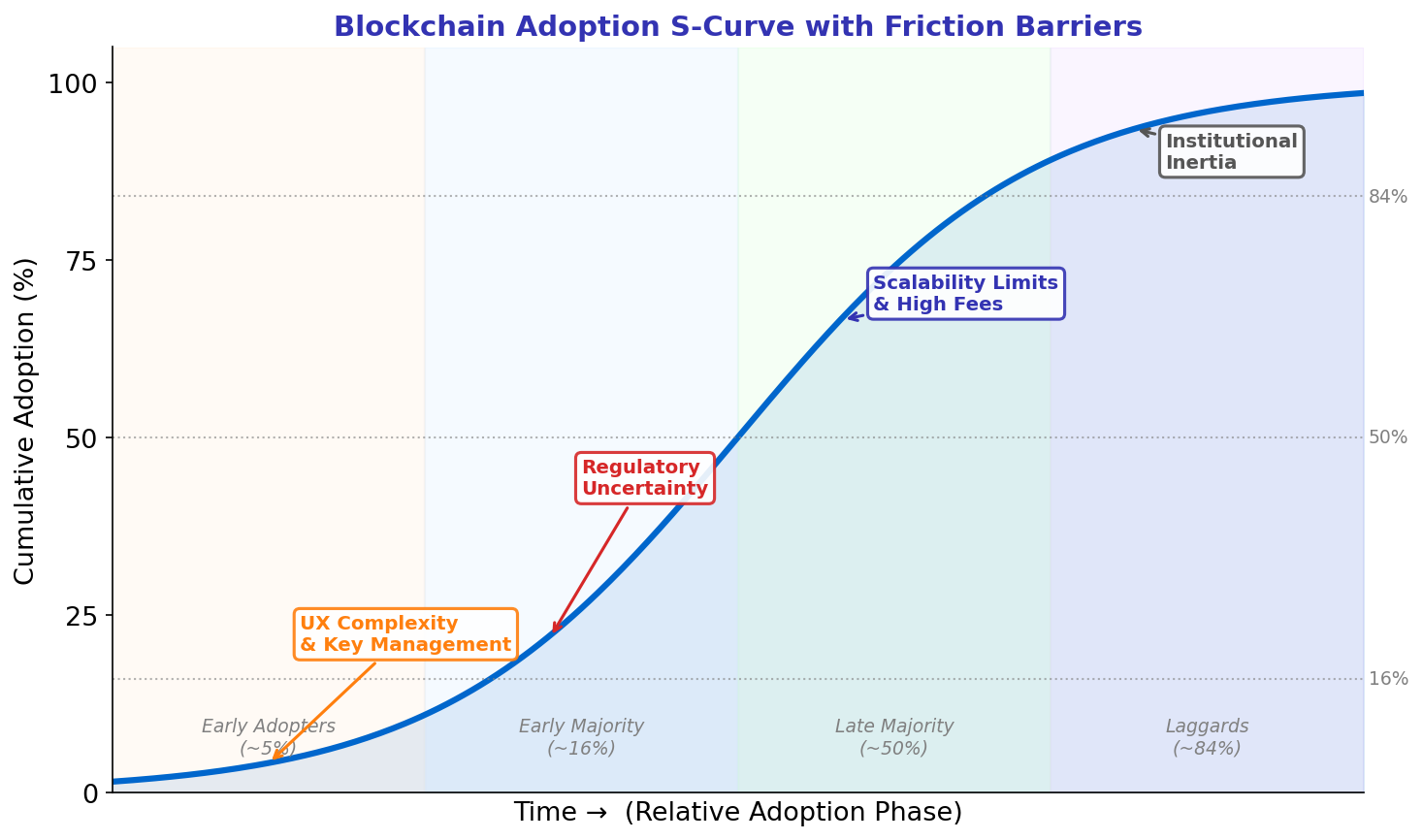
The barriers to mass adoption remain substantial. Self-custody requires users to manage private keys — lose the seed phrase and the funds are permanently inaccessible, with no recovery mechanism. Wallet UX, while improving, remains unintuitive compared to mobile banking apps refined over a decade. Gas fee volatility during network congestion creates unpredictable transaction costs. Phishing attacks, rug pulls, and smart contract exploits expose technically unsophisticated users to losses that would trigger regulatory investigations if perpetrated by traditional financial institutions. Closing the gap between blockchain’s theoretical properties and the user experience that makes them accessible is the defining engineering challenge of the current decade.
Scams, Inequality, and Centralization Paradoxes
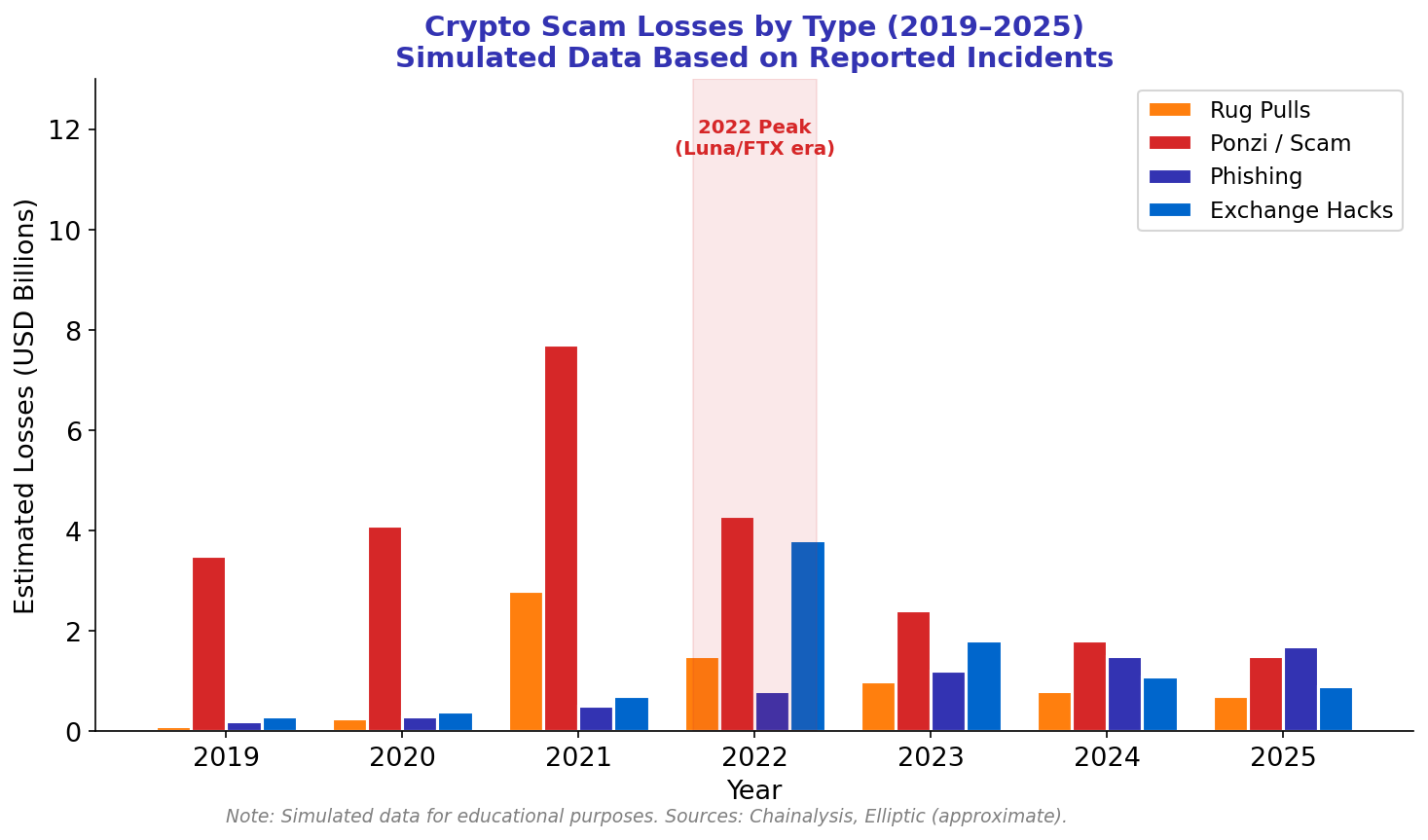
06Blockchain’s worst critics and its worst actors share a common method: overpromising. The technology’s complexity creates information asymmetries that scammers exploit with precision. The Federal Trade Commission reported that Americans lost over $1 billion to cryptocurrency scams in 2022 alone — and that figure captures only reported US losses. Globally, Chainalysis estimates crypto scam revenues exceeded $7 billion in 2022. Understanding the taxonomy of fraud is as important for practitioners as understanding the technology itself.
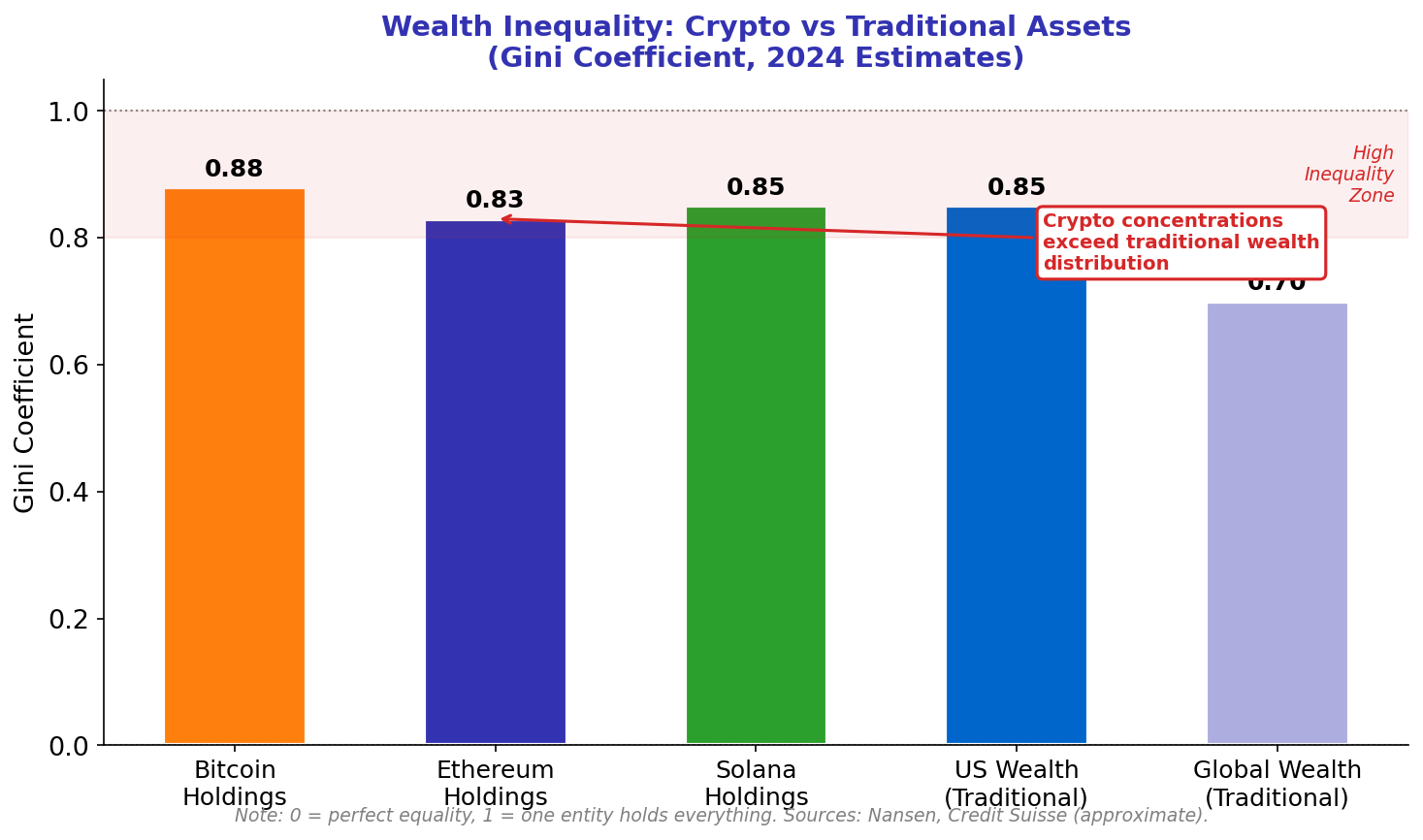
Perhaps more structurally troubling than outright fraud is the wealth concentration that empirical data reveals within crypto markets. Despite the egalitarian rhetoric of decentralized money, Bitcoin’s distribution is among the most concentrated of any asset class studied. The top 1% of Bitcoin addresses hold approximately 28% of all supply. The top 2% of Ethereum addresses control over 70% of staked ETH in the post-Merge validator set. These figures mirror or exceed wealth concentration in traditional financial systems — the difference being that crypto concentration emerged in years rather than centuries.
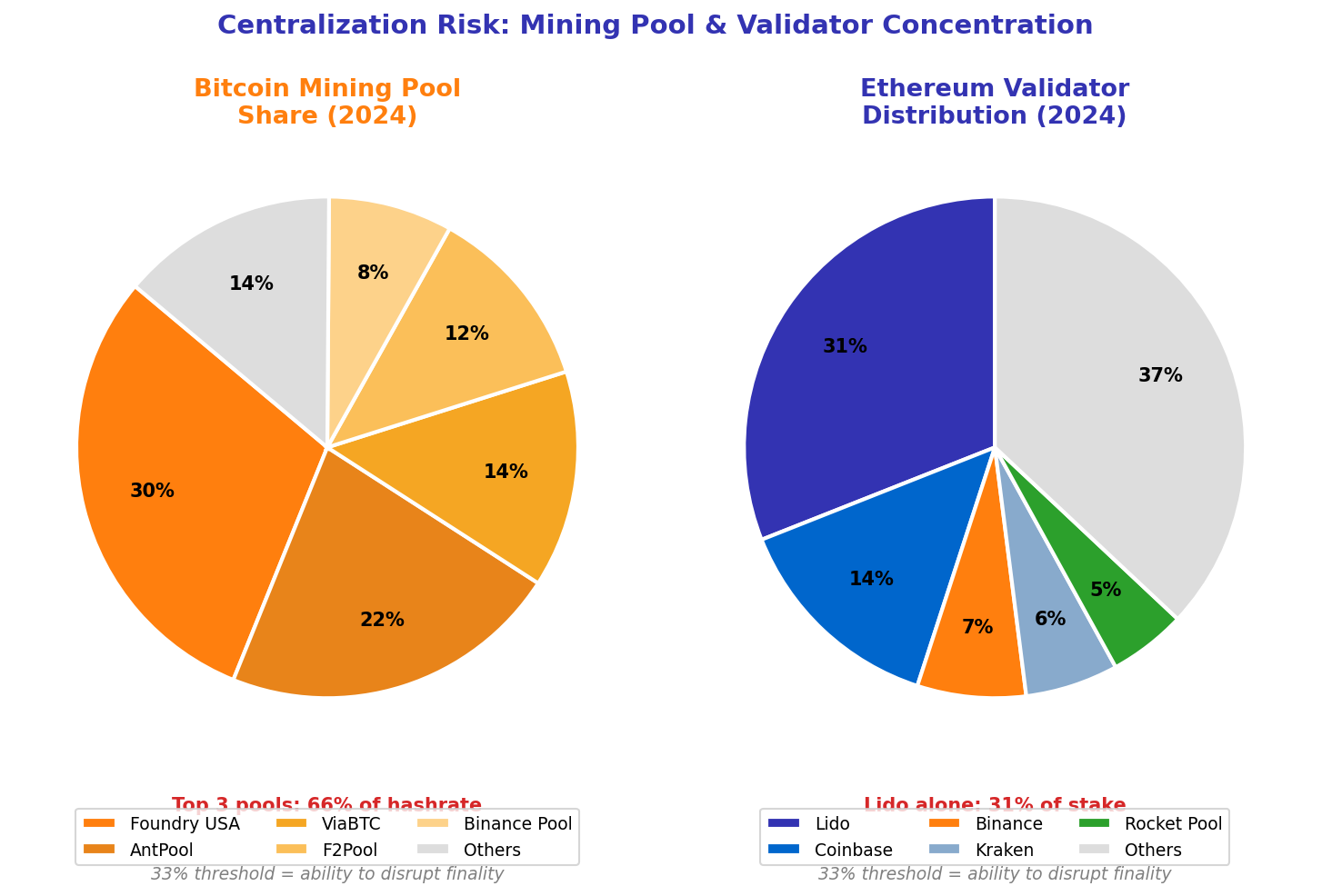
The centralization paradox extends beyond wealth. Bitcoin mining has consolidated into roughly five major pools that collectively control 80%+ of hash rate. Ethereum’s validator set is dominated by liquid staking protocols, with Lido controlling over 30% of staked ETH at various points — approaching the one-third threshold that could enable consensus manipulation. Stablecoin infrastructure depends on Tether and USDC, both centrally managed by commercial entities with the ability to freeze addresses. The infrastructure of “decentralized” finance rests, at multiple layers, on concentrated intermediaries. This is not hypocrisy — it is the predictable result of efficiency pressures operating on systems without adequate decentralization incentives at those layers.
Future Scenarios: Technology Maturity and Possible Trajectories
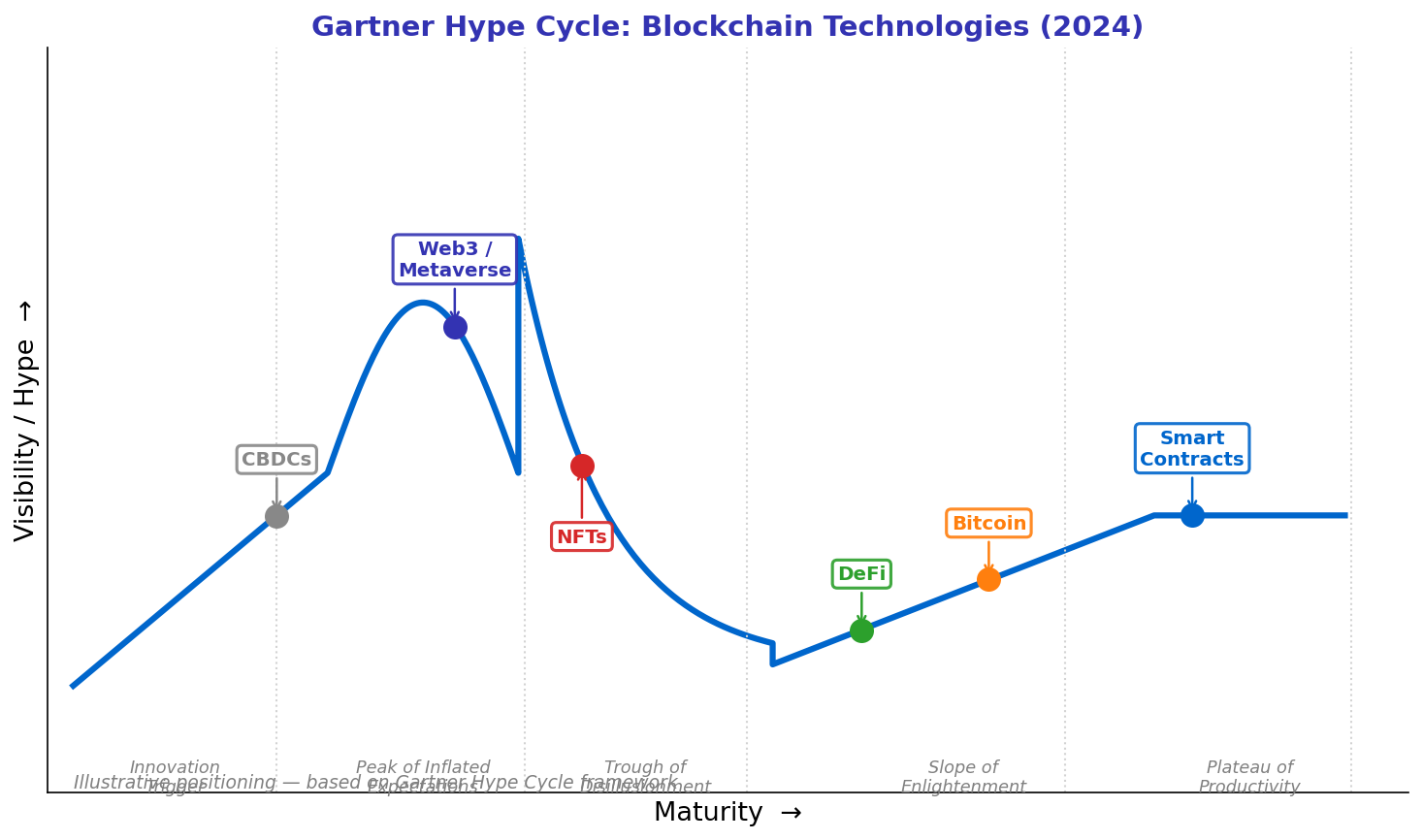
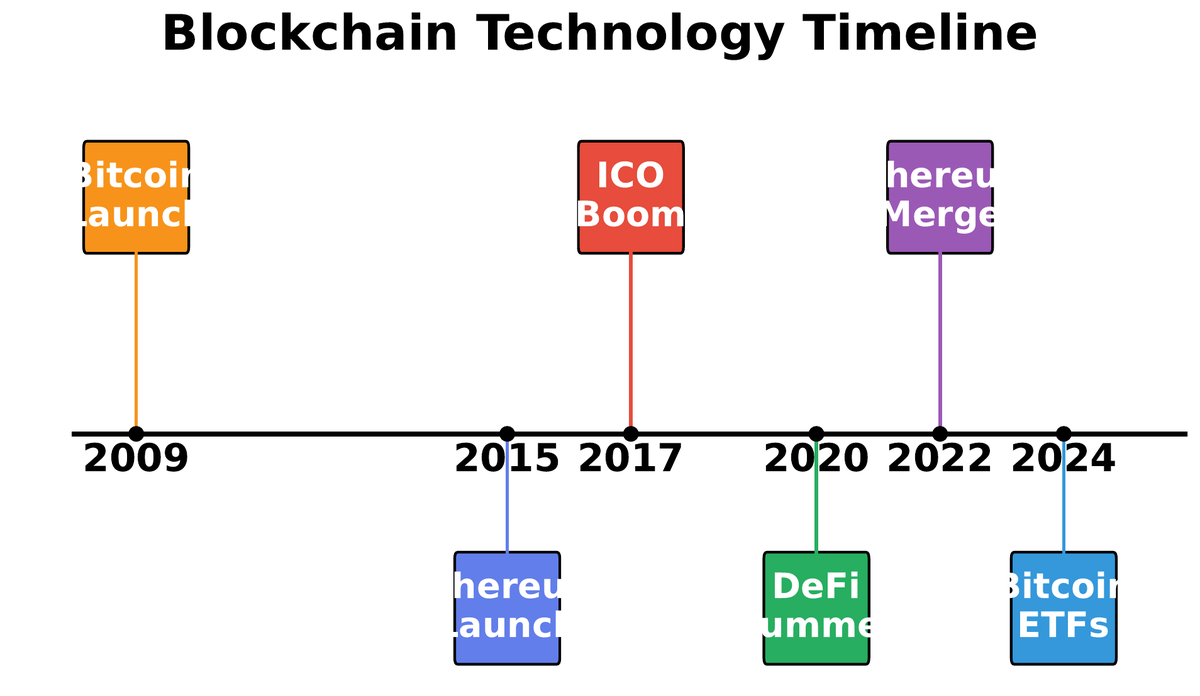
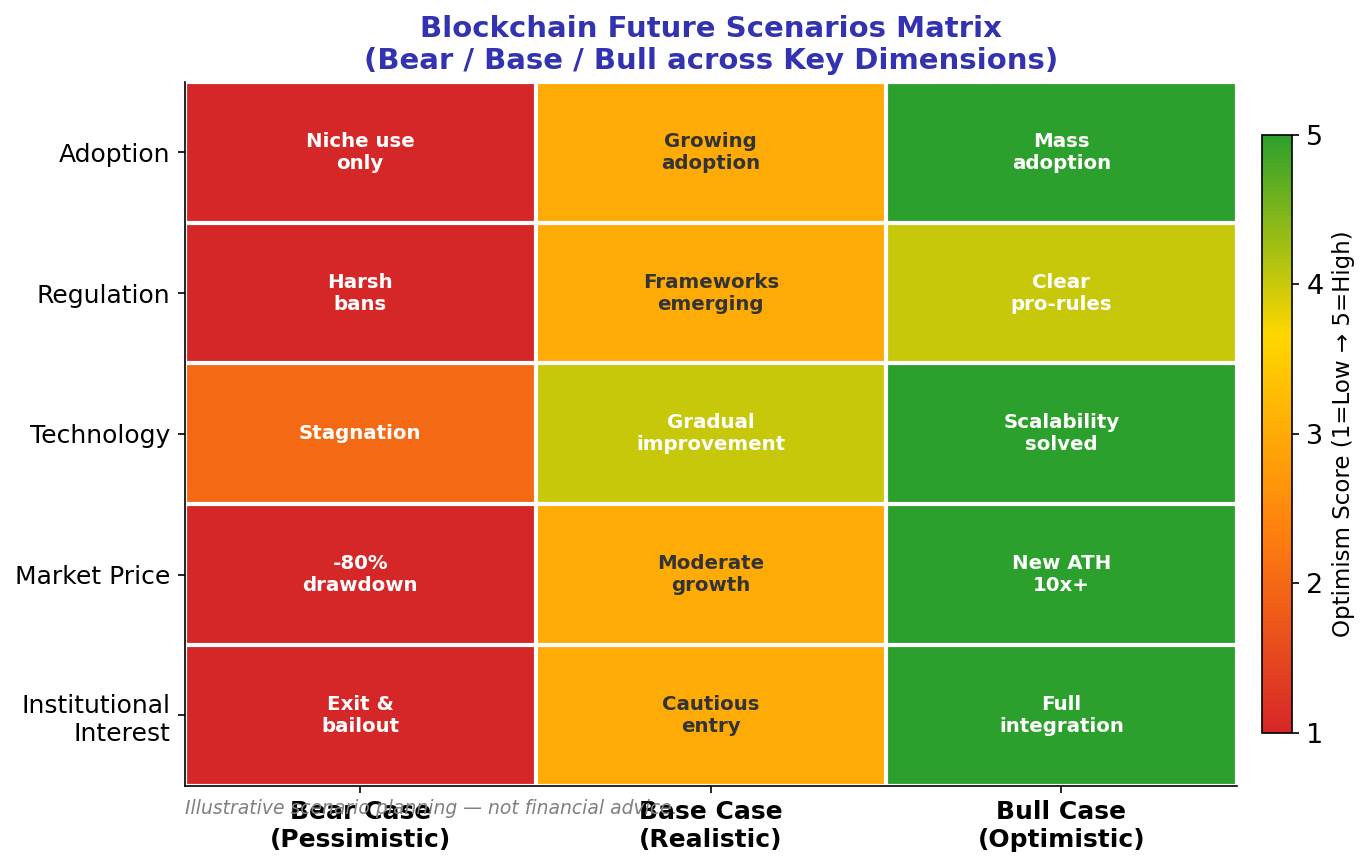
07Forecasting blockchain’s trajectory requires separating the technological development curve from the regulatory environment curve from the market adoption curve — three variables that interact but evolve on different time scales. The Gartner Hype Cycle framework offers a rough map: blockchain passed through a peak of inflated expectations around 2017–2021 and has been navigating a trough of disillusionment since. The question is whether it is climbing the slope of enlightenment toward a plateau of productivity, or whether the trough deepens further before recovery.
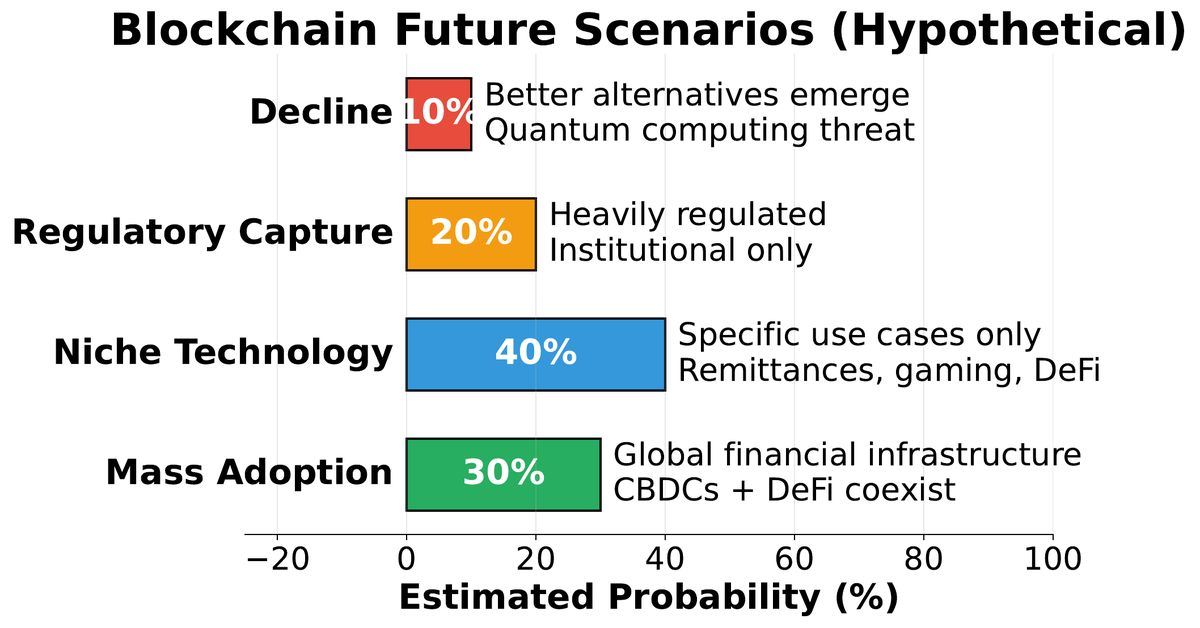
Bull Scenario
L2 rollups reach 1M+ TPS, UX reaches parity with Web 2.0 apps, regulatory clarity attracts trillions in institutional capital, DeFi becomes a genuine alternative to TradFi rails.
Base Scenario
Bitcoin consolidates as institutional digital gold. Ethereum enables niche but real DeFi and NFT markets. Most enterprise blockchain pivots to permissioned systems. Crypto remains a 1–3% portfolio allocation.
Bear Scenario
Hostile regulation in G7 nations constrains growth. CBDCs crowd out stablecoins. Quantum computing threatens current cryptographic assumptions earlier than expected. Only Bitcoin survives as a niche store of value.
Near-term technological developments with high probability of impact include account abstraction (ERC-4337 on Ethereum), which eliminates the seed phrase management problem for ordinary users by enabling smart contract wallets with social recovery. Zero-knowledge rollups are rapidly closing in on general-purpose computation with privacy properties that Base, Optimism, and Arbitrum OP stacks cannot provide. Restaking protocols (EigenLayer) are creating new economic primitives that extend Ethereum’s security to other protocols — though they also create new systemic risks through correlated validator slashing.
Critical Thinking: Forming Evidence-Based Views
08The most dangerous opinions about blockchain are formed in the absence of primary sources. Most media coverage — positive and negative — relies on second-hand accounts, selectively quoted statistics, and sources with financial stakes in a particular narrative. Forming a defensible view requires going deeper: reading whitepapers, examining on-chain data, understanding the incentives of information sources, and applying consistent analytical standards to all claims regardless of which “side” makes them.
1. Who benefits if this claim is believed? Promoters have financial incentives; critics may have regulatory or competitive incentives. Map the incentives first.
2. Is this a claim about technology or about markets? Technology properties are verifiable; market predictions are speculative. Treat them differently.
3. Is the comparison fair? Comparing Bitcoin transaction energy to Visa transaction energy ignores settlement finality; comparing banking system energy to Bitcoin ignores scale. Fair comparisons are hard to find and easy to fabricate.
4. What does the on-chain data say? Blockchain’s transparency is a research resource. Etherscan, Dune Analytics, Glassnode, and Chainalysis provide primary data that sidesteps narrative framing.
5. What is the counterfactual? Blockchain alternatives are not free. The alternative to DeFi is TradFi with its own exclusions and costs. The alternative to PoW is PoS with its own centralization dynamics. Always compare to realistic alternatives.
• PoW Bitcoin uses significant energy; the renewable fraction is disputed but real
• Ethereum’s Merge proved PoS can secure large networks
• Stablecoin adoption in emerging markets is measurably large
• DeFi protocols have facilitated billions in genuine economic activity
• Regulatory fragmentation creates real compliance costs for operators
• “Blockchain eliminates the need for trust” (replaces one trust model with another)
• “Crypto will bank the unbanked” (requires smartphone, internet, crypto literacy)
• “Smart contracts are self-executing and autonomous” (execution requires gas; code has bugs)
• “DeFi is fully decentralized” (admin keys, oracle dependencies, concentrated validators)
• “Bitcoin is worthless / Bitcoin is digital gold with no counterpart risk” (both extremes ignore evidence)
You have now completed twelve lectures covering Bitcoin’s cryptographic foundations, Ethereum’s computation model, DeFi protocols, NFTs, DAOs, Layer 2 scaling, cross-chain bridges, and the contested debates surveyed here. The field continues to evolve rapidly — new consensus mechanisms, new regulatory frameworks, new applications. The invariant skill across all of this change is the ability to evaluate technical claims with rigor and to ask whose interests are served by a particular framing. That capacity for independent analysis is more durable than any specific protocol knowledge, and it is what this course has ultimately been designed to develop.
Good luck with your projects. The best engineers in this space will be those who understand both the cryptographic machinery and the human systems — economic, regulatory, and social — in which that machinery operates. Both perspectives are necessary. Neither is sufficient alone.