L04: Consensus Mechanisms
The Problem: Agreeing Without a Referee
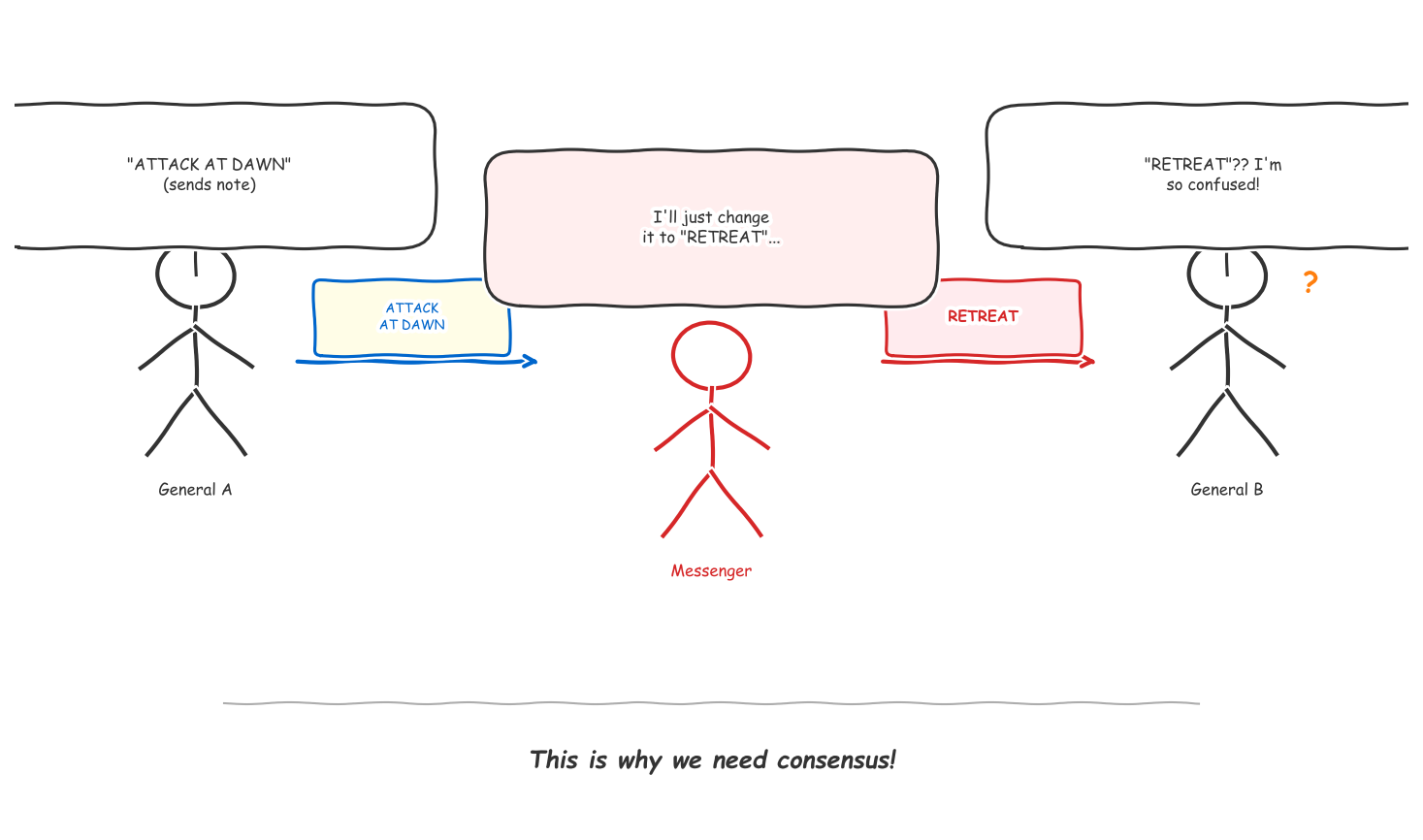
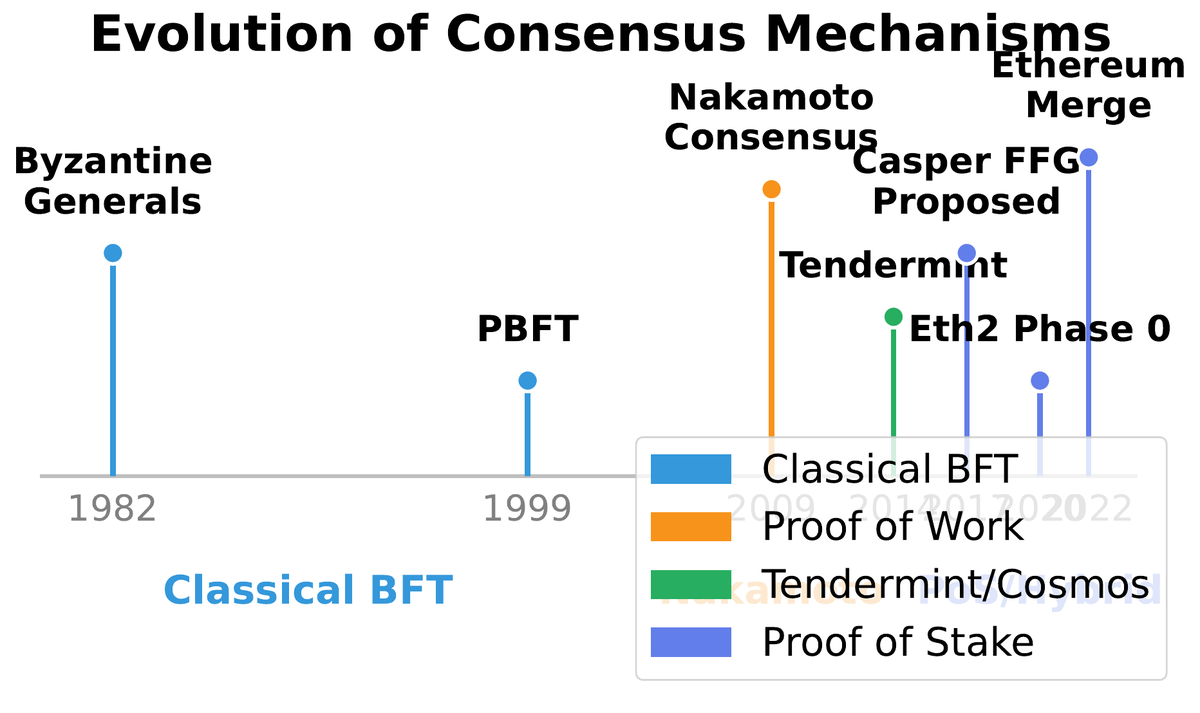
01Consider a scenario with five generals surrounding a city. They must all attack simultaneously to succeed, but can only communicate by messenger. Some generals may be traitors who send conflicting messages. The question — formalized by Lamport, Shostak, and Pease in their landmark 1982 paper — is: can the loyal generals coordinate reliably despite treacherous colleagues and unreliable communication channels? This is the Byzantine Generals Problem, and it is not merely a military metaphor. It is the formal statement of what every blockchain must solve.
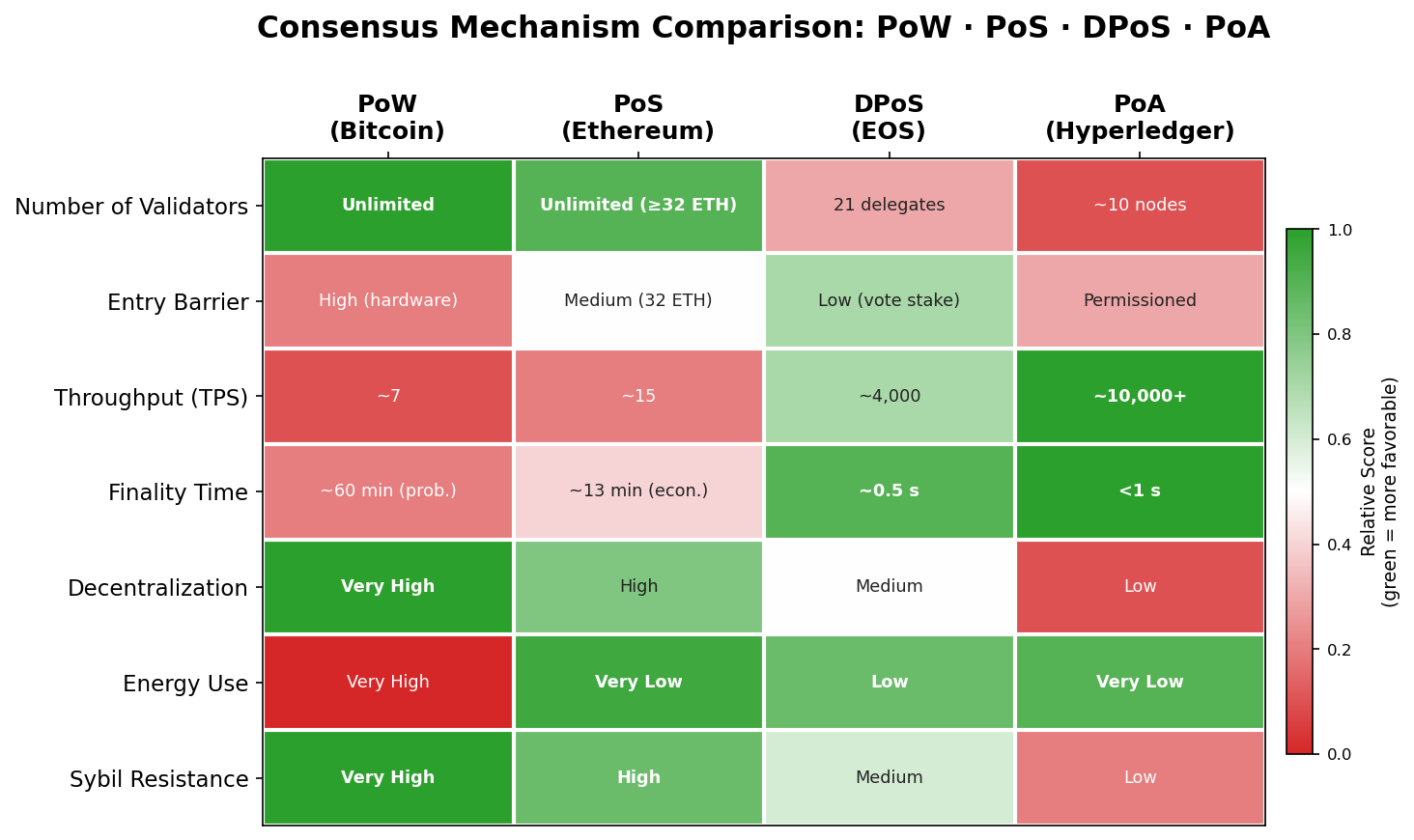
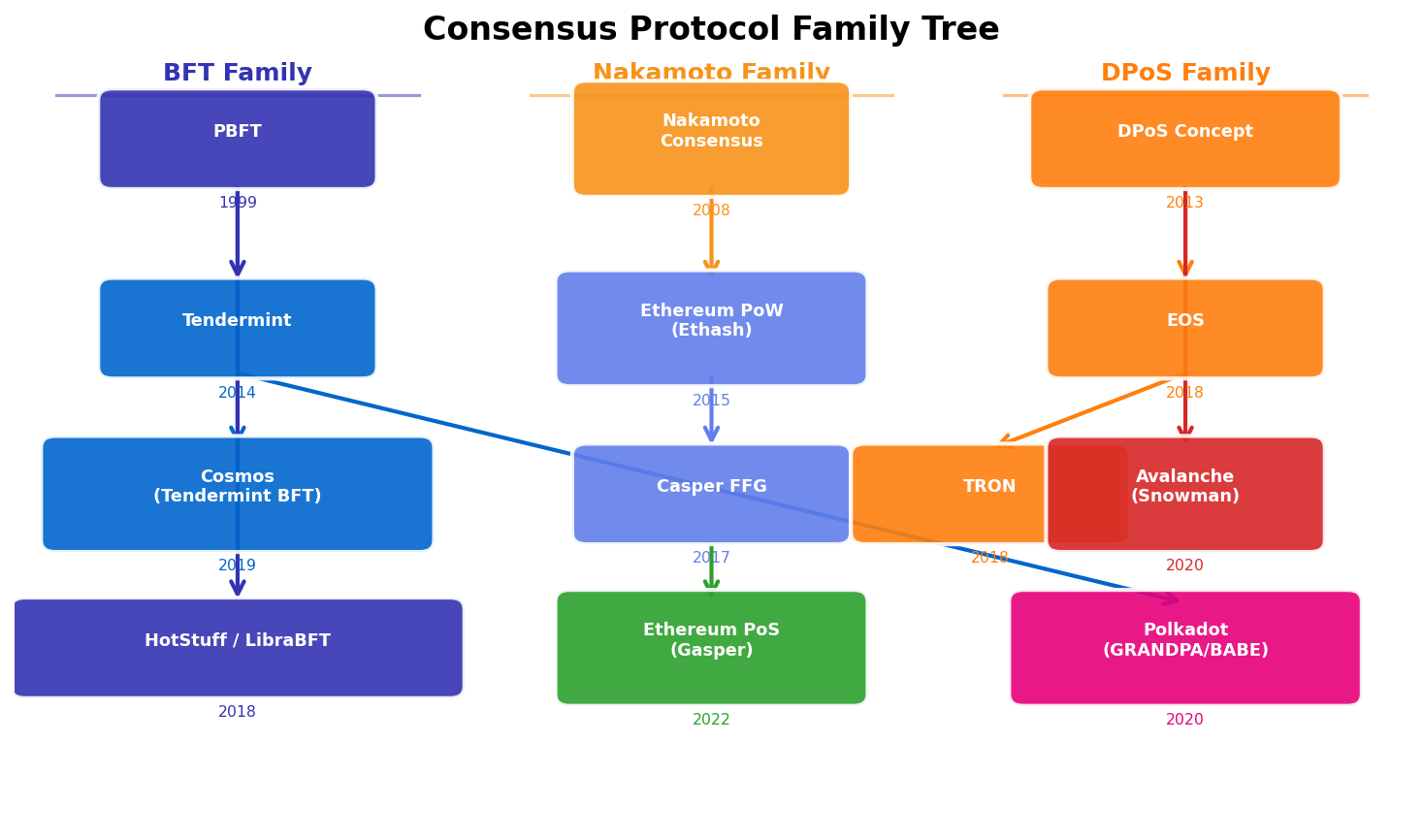
In a distributed ledger, nodes replace generals, network packets replace messengers, and malicious validators replace traitors. The ledger’s integrity depends entirely on a majority of participants agreeing on which transactions occurred, in which order, and which blocks are valid — all without any single node having authority over the others. Before Bitcoin, classical Byzantine Fault Tolerant (BFT) systems solved this in closed, permissioned settings where all participants were known in advance. Nakamoto’s insight was to extend the problem to a permissionless, open network where anyone can join anonymously.
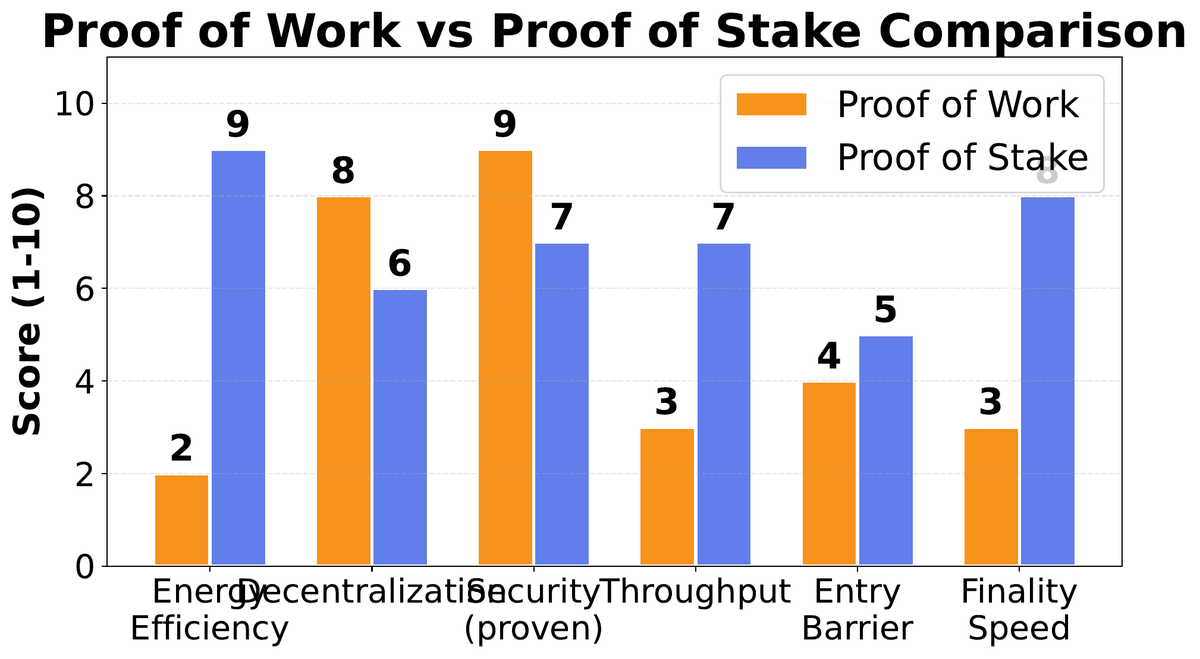
The practical consequence is that blockchain consensus mechanisms are not trying to achieve perfection — they are choosing which failure mode is most acceptable. Proof of Work accepts the possibility that two honest miners find blocks simultaneously, creating a temporary fork that resolves probabilistically. Proof of Stake with BFT accepts the possibility that the chain halts if too many validators go offline, rather than risk producing conflicting finalized blocks. Understanding why these trade-offs exist is the foundation for evaluating any consensus mechanism you will encounter in practice.
Fundamentals: Safety, Liveness, and Finality
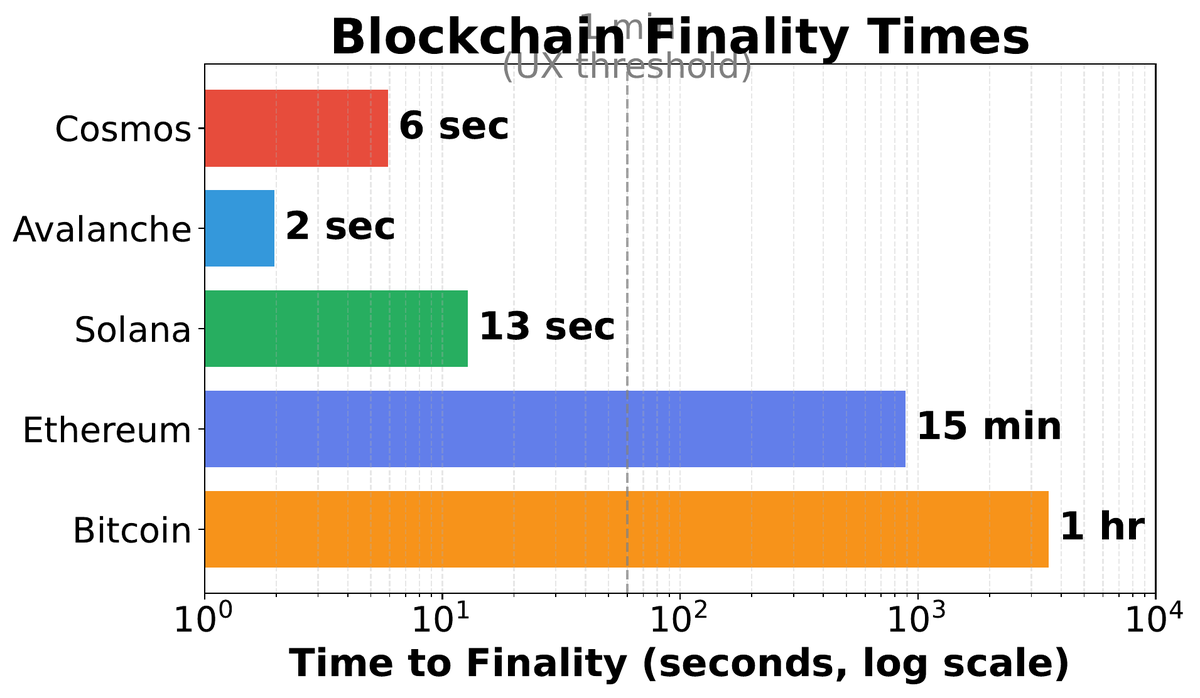
02Consensus protocols are characterized along three axes. Safety means that no two honest nodes will ever permanently commit to conflicting versions of history — all honest nodes will ultimately agree on the same chain. Liveness means the system continues to make progress and does not stall indefinitely. Finality describes the point at which a committed transaction becomes irreversible, either in a probabilistic sense (increasingly unlikely to reverse) or an absolute sense (mathematically provable).
These properties interact in a fundamental tension. Prioritizing safety tends to sacrifice liveness: a protocol that refuses to finalize without 2/3 agreement will halt if validators go offline. Prioritizing liveness tends to sacrifice safety: a protocol that always makes progress may produce temporary forks and require a post-hoc fork choice rule to determine the “real” chain. Nakamoto consensus deliberately sacrifices deterministic finality for liveness — Bitcoin always makes progress and never halts, but transactions are only probabilistically final.
| Protocol | Finality Type | Fault Tolerance | Permissionless | Throughput | Used By |
|---|---|---|---|---|---|
| Nakamoto PoW | Probabilistic | 50% hashrate | Yes | 3–7 TPS | Bitcoin, Litecoin |
| Casper FFG + LMD-GHOST | Economic (2 epochs) | 33% stake | Yes | 15–100 TPS | Ethereum post-Merge |
| Tendermint / CometBFT | Instant (1–7s) | 33% validators | No (known set) | 1,000–10,000 TPS | Cosmos, Celestia |
| DPoS (EOS-style) | Semi-final (2 rounds) | 33% delegates | Delegated only | 1,000–4,000 TPS | EOS, TRON |
| Proof of Authority | Instant | 50% authorities | No | 100–300 TPS | Private chains, testnets |
Proof of Work: Energy as Security
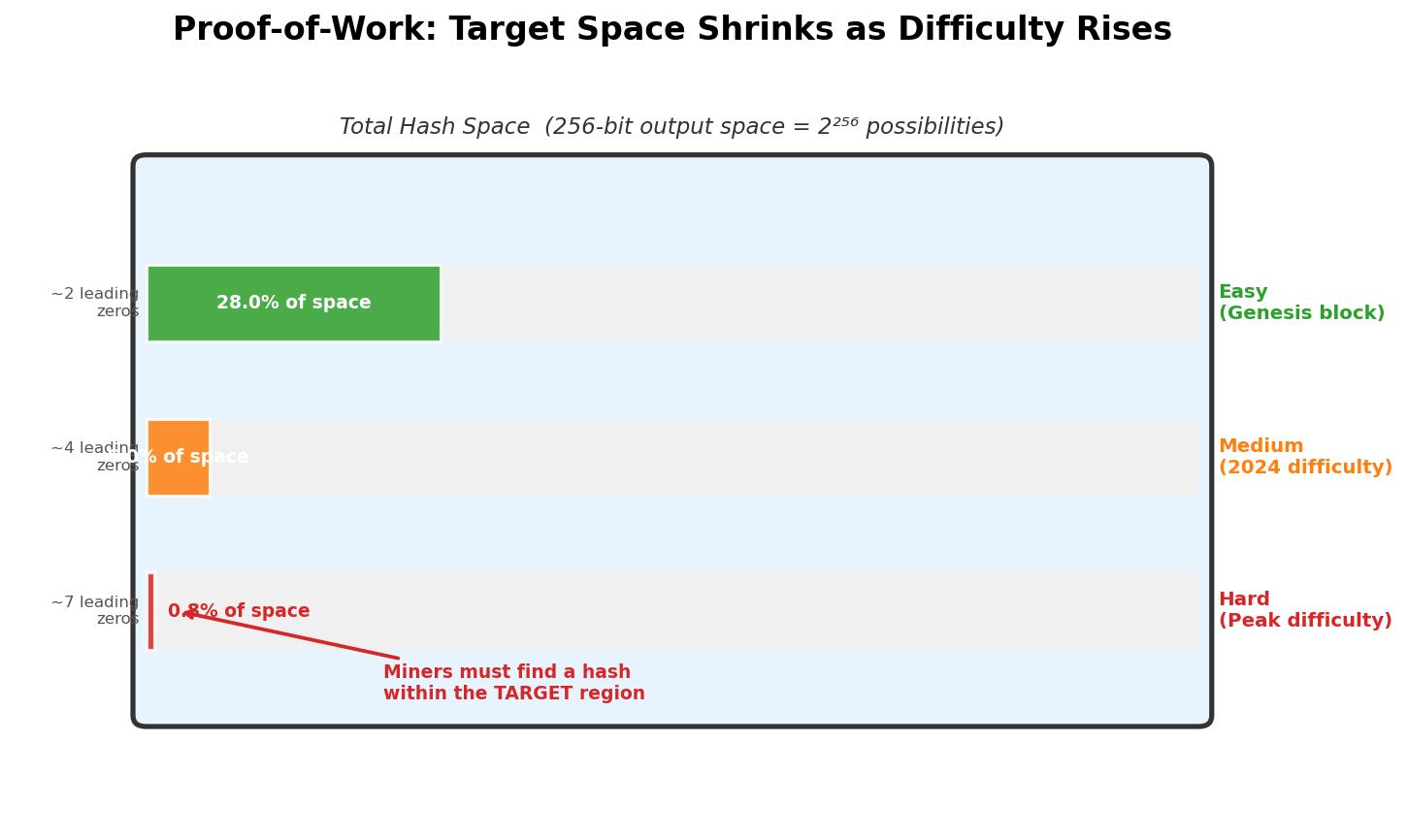
03Nakamoto consensus solved the Byzantine Generals Problem for an open, permissionless network by replacing identity with computation. Instead of requiring nodes to identify themselves — which would enable Sybil attacks where one adversary creates millions of fake identities — each node must demonstrate expenditure of real-world resources. Mining is a probabilistic lottery: miners repeatedly hash a block header with incrementing nonces until the output falls below a difficulty target. The winning miner broadcasts their block and claims the block reward.
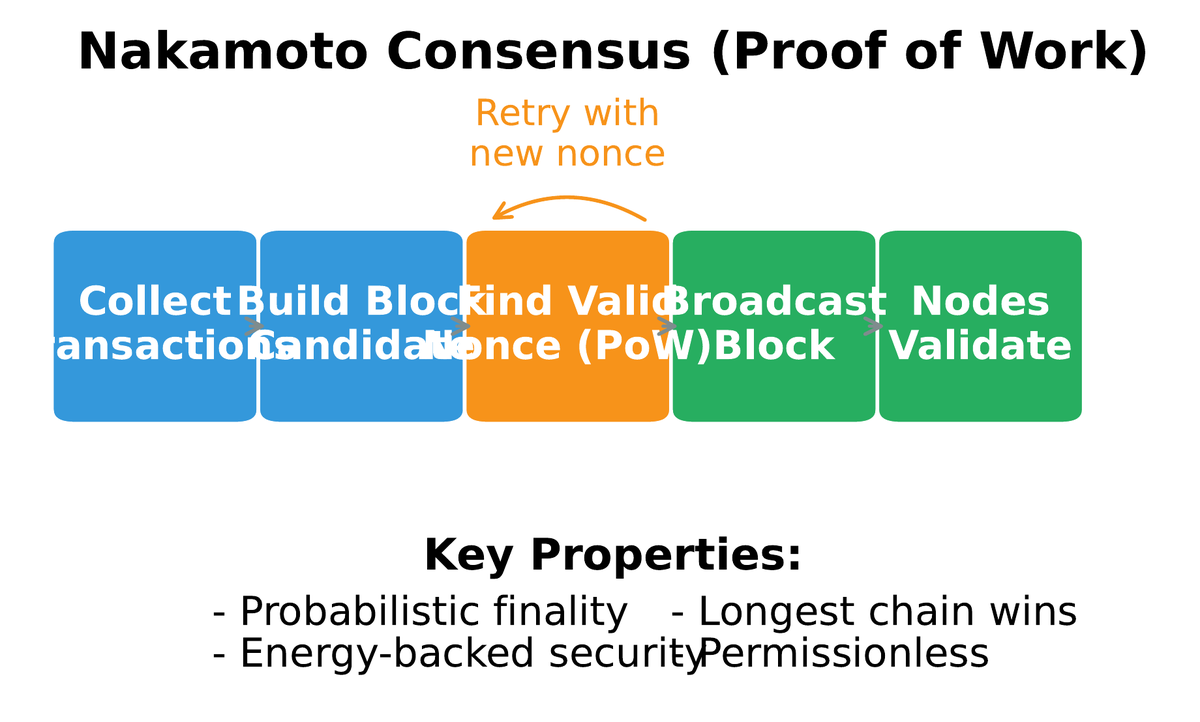
The elegance lies in the self-adjusting difficulty mechanism. Bitcoin recalibrates its target every 2016 blocks (approximately two weeks) so that average block time stays close to 10 minutes regardless of total network hash rate. This means that if millions of new miners join the network overnight, blocks temporarily arrive faster until the next adjustment, at which point the puzzle becomes harder to compensate. The adjustment mechanism is a negative feedback loop that keeps the block schedule stable across orders of magnitude of hash rate variation.
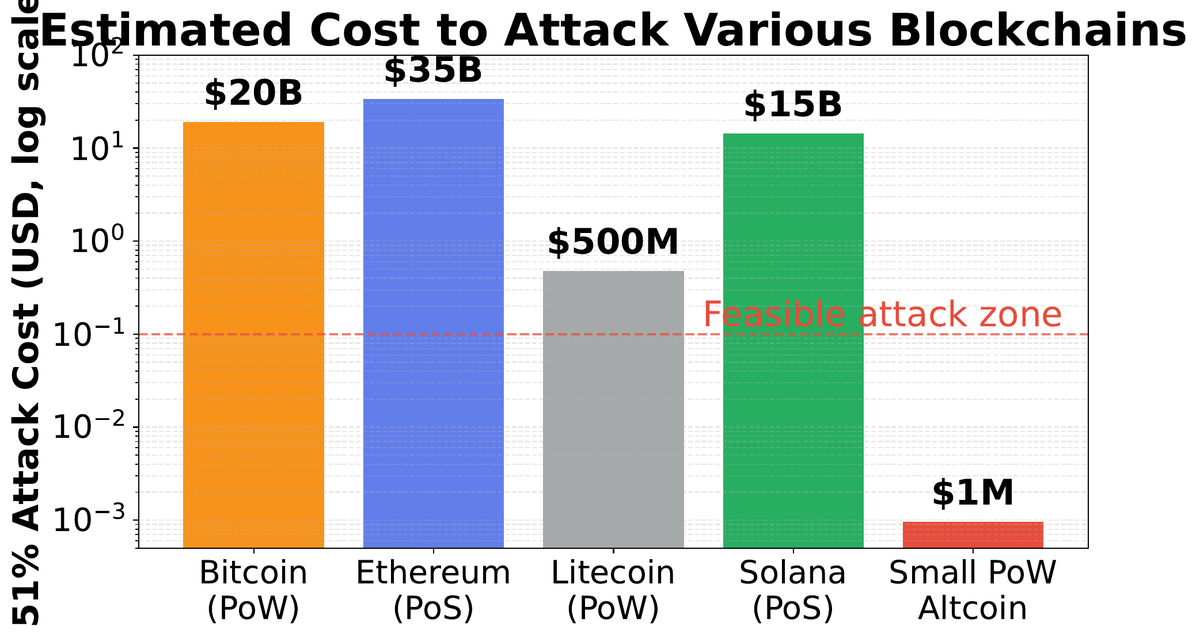
The security model is stark and empirically verifiable: the cost of attacking Bitcoin is approximately equal to the cost of acquiring and operating more than 50% of its hash rate for the duration of the attack. As of 2024, Bitcoin’s hash rate exceeded 600 exahashes per second — sustained attack would require hardware and electricity expenditure in the tens of billions of dollars, with no guarantee of recovering the investment. This “real resource” backing is what PoW proponents consider its core strength: the chain’s security is grounded in physical reality, not just economic incentives that may unravel in a crisis.
Proof of Stake: Capital as Security
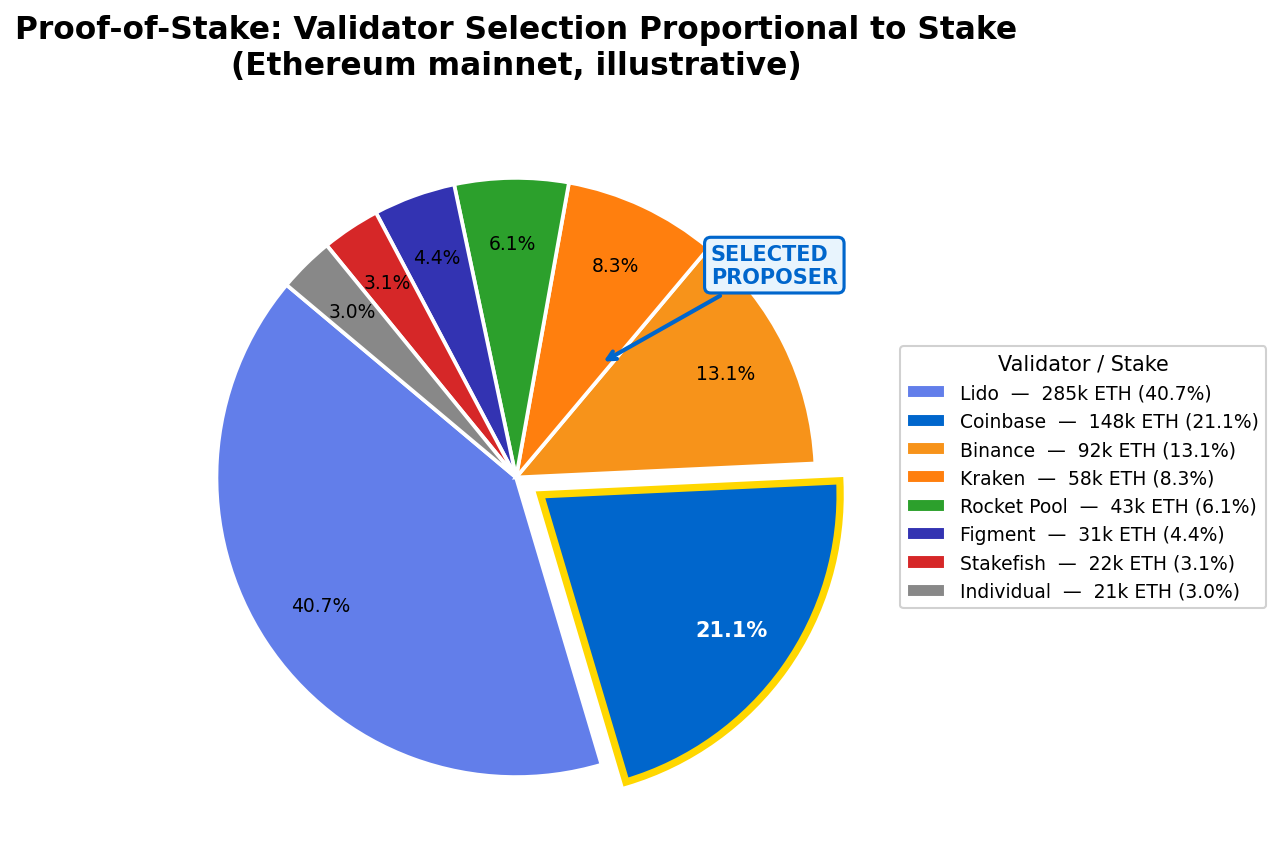
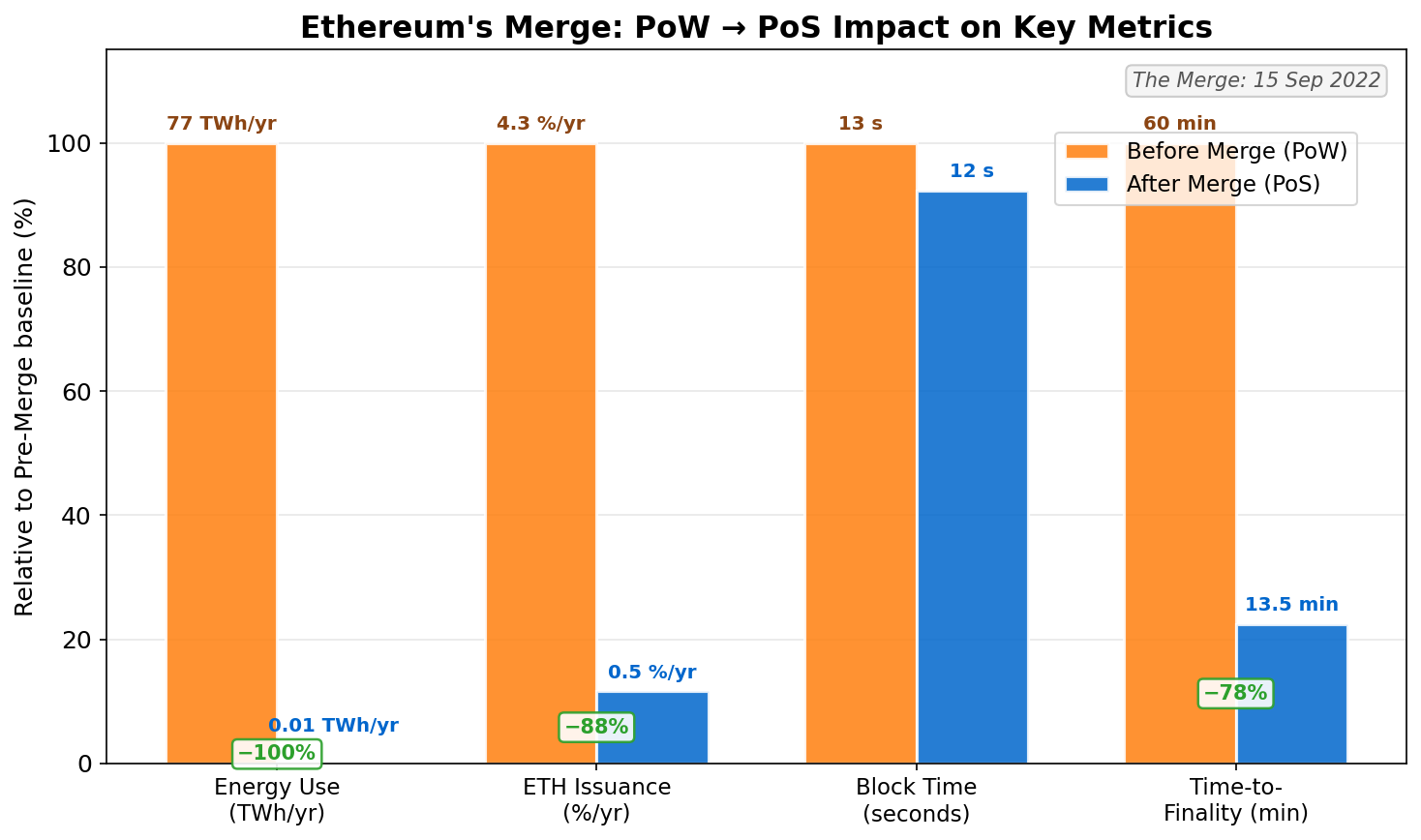
04Proof of Stake replaces physical resource expenditure with economic stake. Validators lock tokens — on Ethereum, a minimum of 32 ETH per validator — into a deposit contract as collateral. The protocol then selects validators to propose and attest to blocks using cryptographic randomness weighted by stake. The key insight is that validators now have skin in the game: if they misbehave, their staked capital is programmatically destroyed through slashing. An attacker must acquire a large fraction of the staked supply, meaning their attack instrument is also their liability.
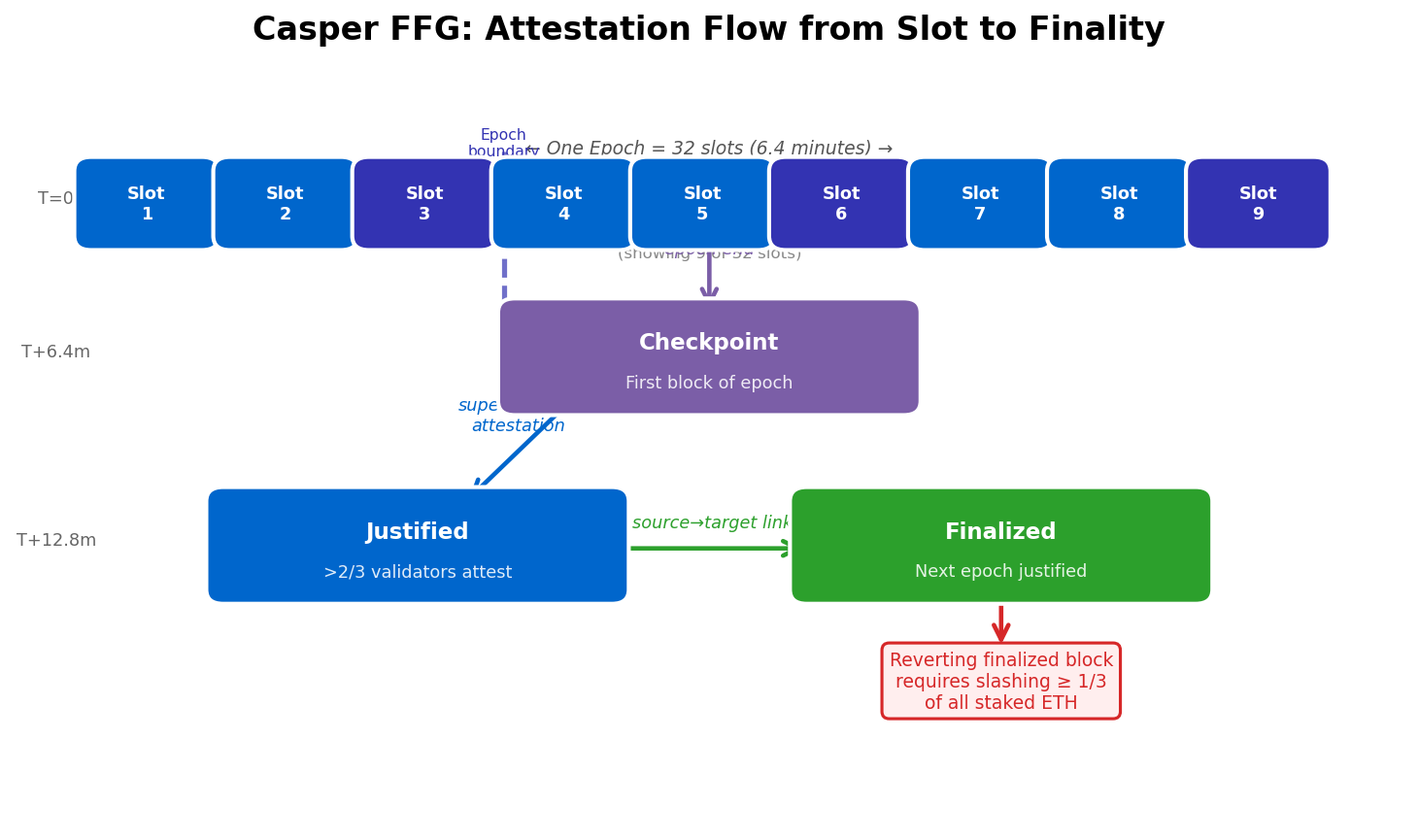
Ethereum’s post-Merge consensus combines two protocols. LMD-GHOST (Latest Message Driven Greediest Heaviest Observed SubTree) is the fork choice rule that ensures liveness: the chain always makes progress by choosing the heaviest subtree of attestations, even without finality. Casper FFG (Friendly Finality Gadget) overlays economic finality: at the end of each 32-slot epoch, a checkpoint can be justified and then finalized if it receives 2/3 of all validator attestations weighted by stake. A finalized block cannot be reverted without burning at least 33% of all staked ETH.
BFT Variants, DPoS, and Tendermint
05The BFT family of protocols predates blockchain by three decades. Classical BFT systems like PBFT (Practical Byzantine Fault Tolerance, Castro & Liskov 1999) provided strong safety guarantees with instant finality but required all participants to know each other and generated O(n²) messages — making them unscalable beyond a few dozen nodes. Modern BFT variants have addressed the scalability bottleneck through threshold signatures, validator committee rotation, and aggregated attestations.
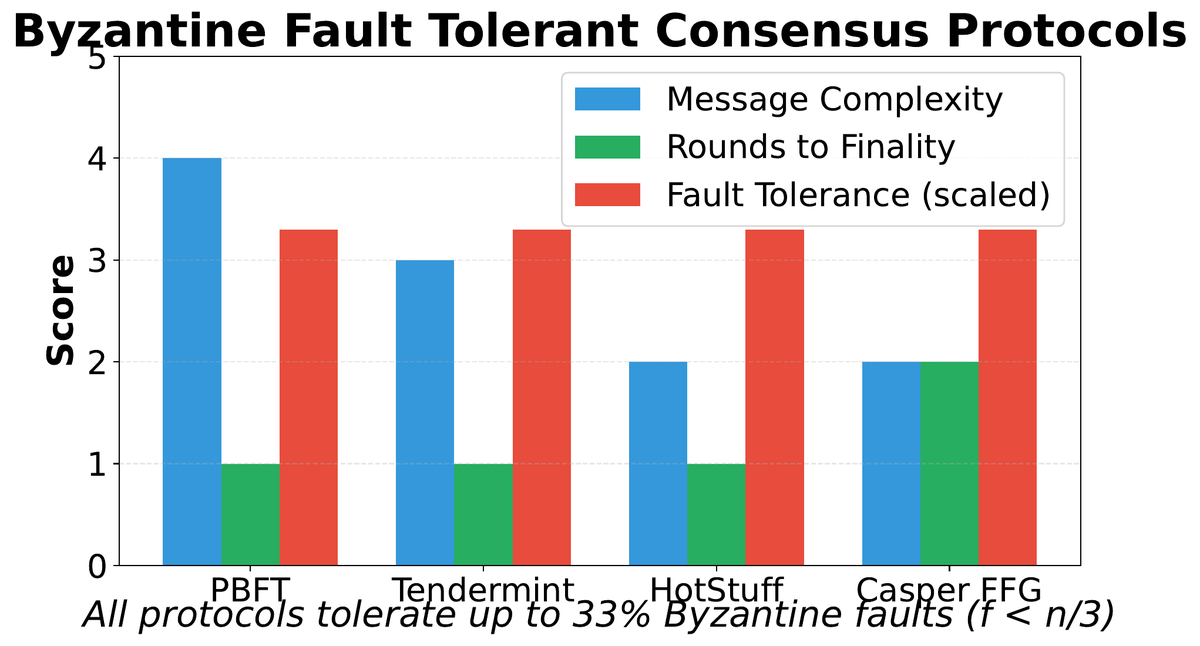
Tendermint (now CometBFT), the consensus engine underlying the Cosmos ecosystem, achieves instant finality with 1–7 second block times by requiring a known, bonded validator set. Each round consists of three phases: Propose (round-robin leader broadcasts a block), Prevote (validators signal readiness), and Precommit (validators lock in). A block is finalized when 2/3 of validators by stake weight have precommitted. If the round fails (insufficient prevotes), a new leader is selected after a timeout. Crucially, Tendermint halts rather than produces conflicting finalized blocks — it prioritizes safety over liveness.
Attacks, Failure Modes, and Structural Limits
06Every consensus mechanism has a well-defined adversarial threshold: the minimum resource an attacker must acquire to break the protocol. Understanding these thresholds — and the costs to reach them — is how practitioners evaluate chain security in practice. A chain is only as secure as the cost of attacking it, not the theoretical guarantees of its protocol specification.
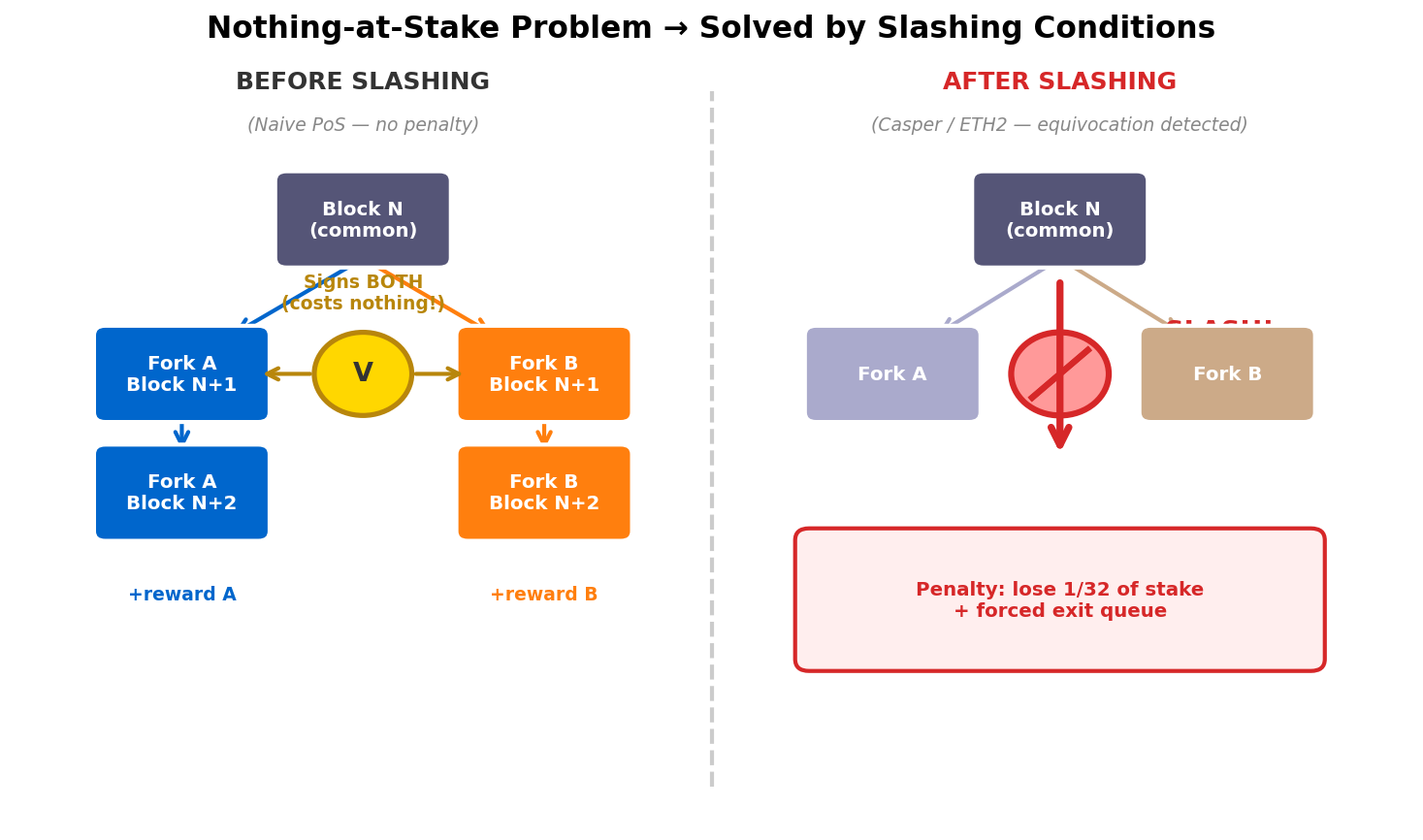
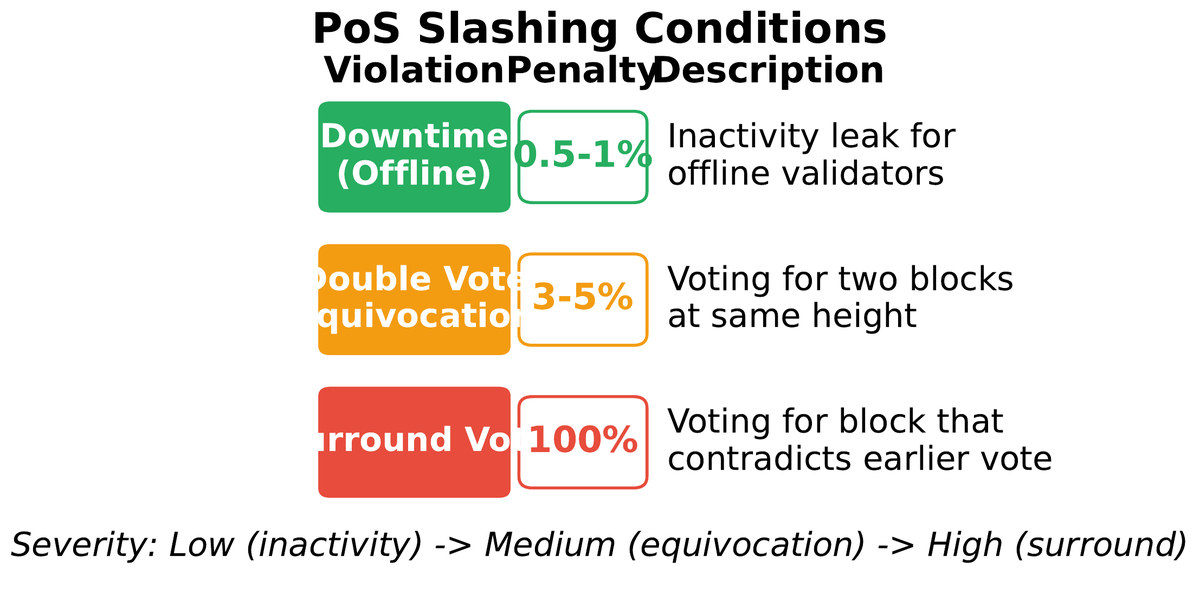
Proof of Stake introduces a structurally different threat: the nothing-at-stake problem. In a naive PoS implementation, validators have no cost to voting on multiple forks simultaneously — if any fork wins, they collect rewards, and if a fork loses, they lose nothing. This means rational validators would always vote on every fork, preventing consensus from converging. The solution is slashing: validators who sign two conflicting blocks at the same height are detected on-chain and a portion of their staked capital is permanently burned.
Long-range attacks present a subtler threat specific to PoS. An adversary who once held a large stake could use their old private keys to construct an alternative history from deep in the past — one that competes with the current canonical chain. Unlike PoW where rewriting history requires re-expending physical energy, old PoS keys carry no ongoing cost. The mitigations are weak subjectivity checkpoints (new nodes must obtain a recent trusted state from a reliable source before syncing) and key-evolving cryptography (old keys are cryptographically retired). These are sound engineering solutions but they do introduce a degree of social trust that pure PoW avoids.
Validator Economics, Slashing, and Stake Concentration
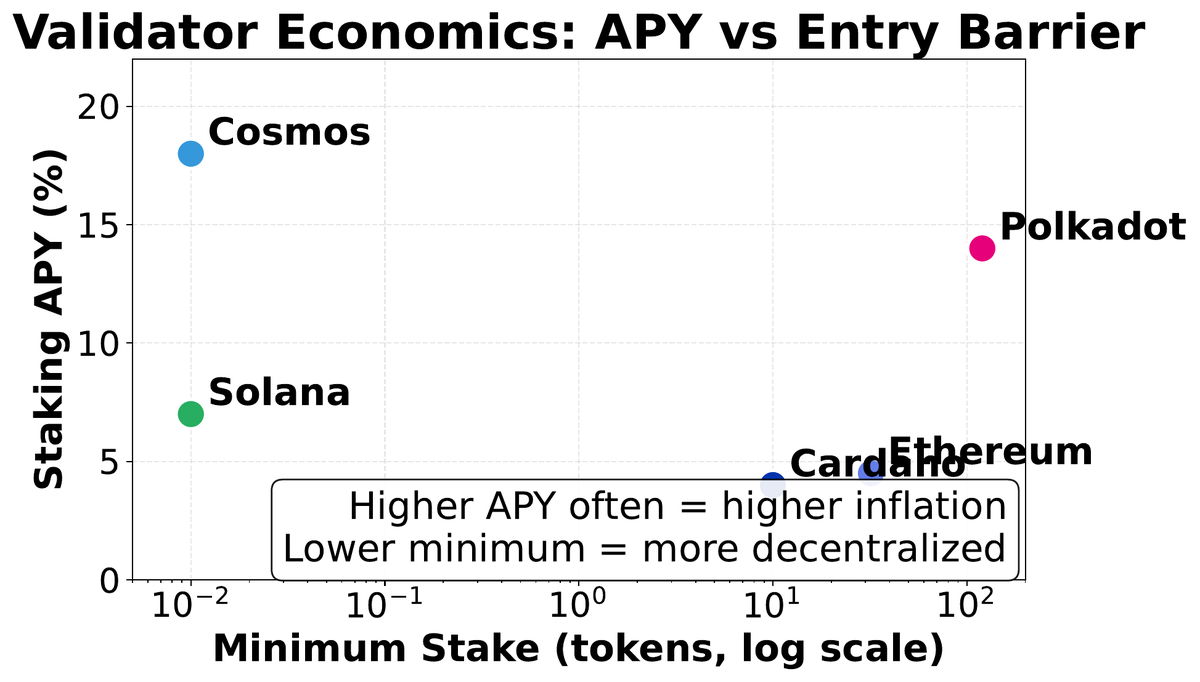
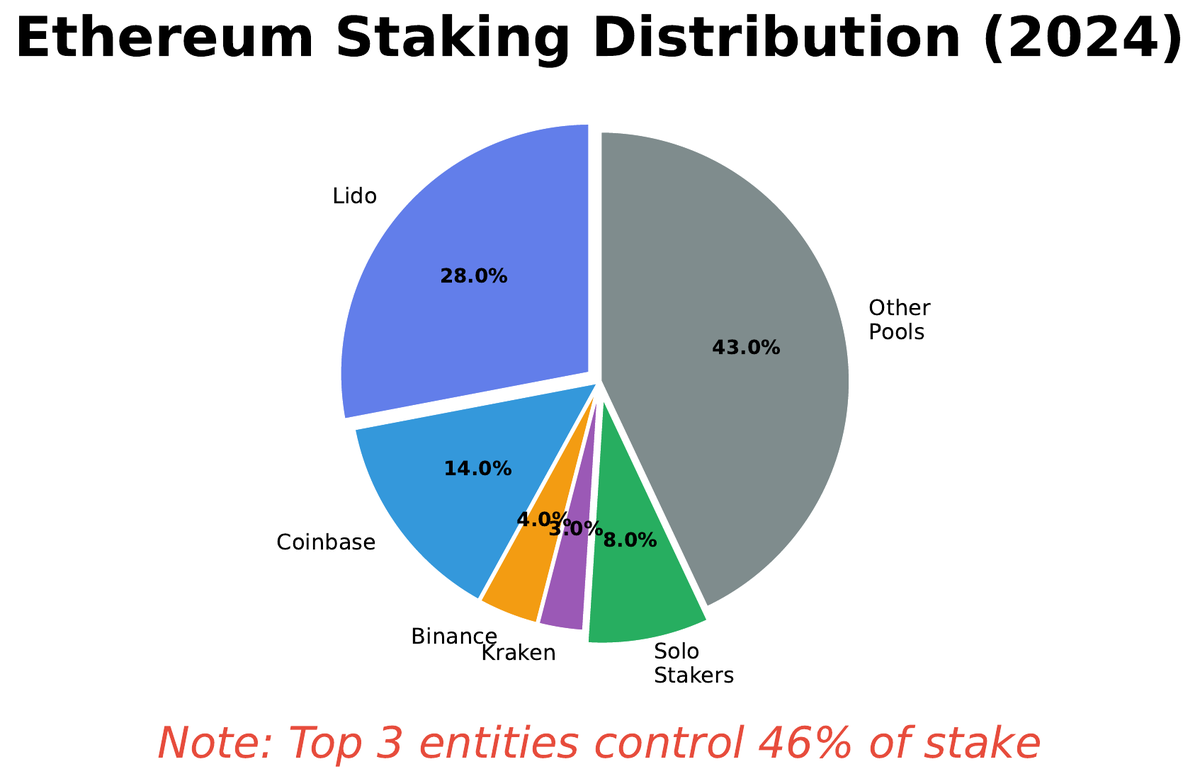
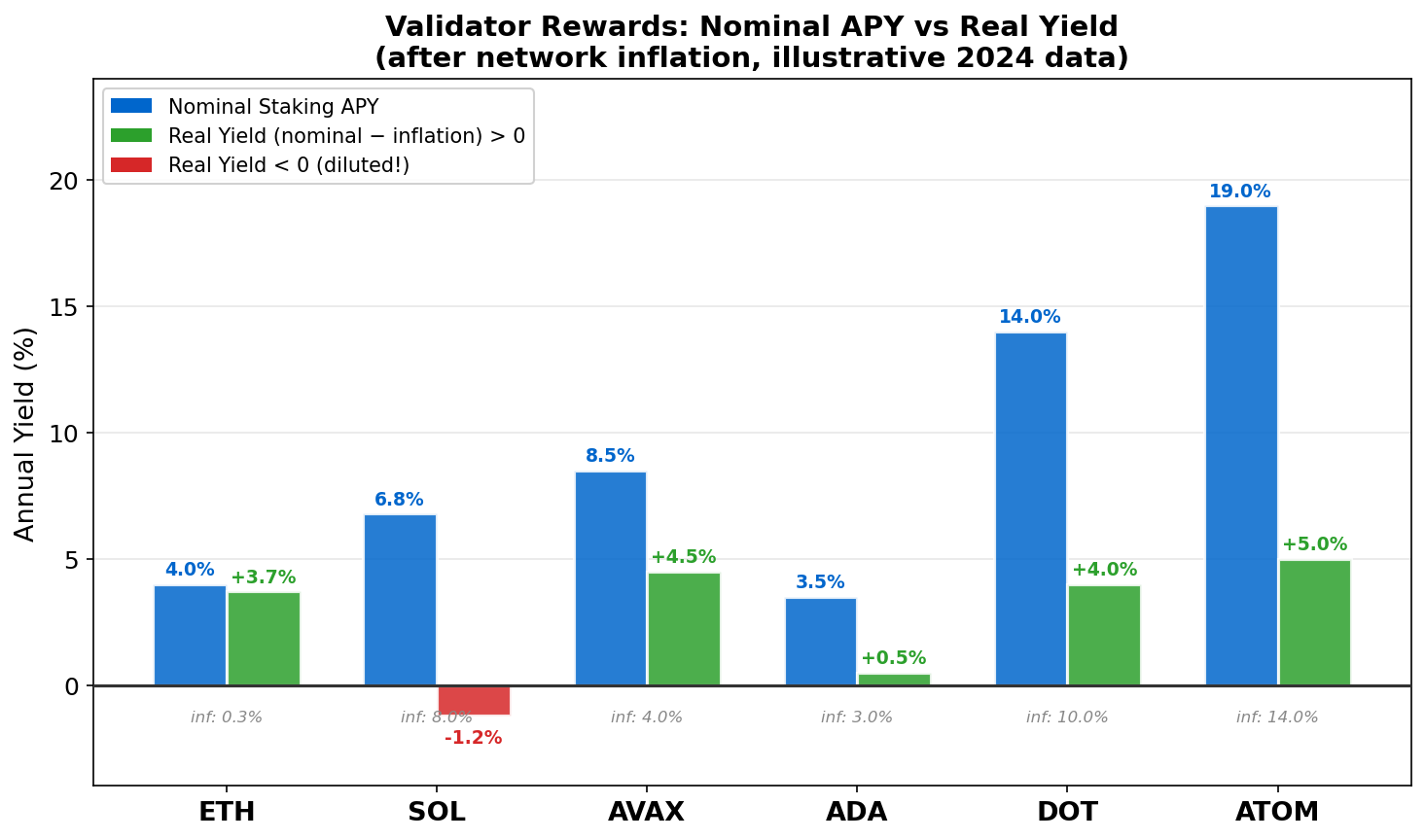
07Consensus mechanisms are not just technical protocols — they define economic systems that determine who profits from block production, how rewards are distributed, and who bears the risk of slashing. These economic incentives shape the long-run security and decentralization of the network in ways that may not be apparent from the protocol specification alone.
In Ethereum’s PoS, validators earn two types of income: consensus layer rewards (for correct attestations, calculated as a function of the total staked ETH) and execution layer rewards (transaction priority fees and MEV, which flow to the validator who proposes the block). The base issuance rate scales inversely with the square root of total stake — if more validators join, the per-validator APY falls, creating a natural equilibrium that prevents the staking ratio from reaching 100%.
Slashing penalizes two specific equivocation behaviors: double voting (signing two different blocks for the same slot) and surround voting (signing an attestation that surrounds or is surrounded by a previous attestation, enabling long-range attack vectors). On Ethereum, a first-time slashing event penalizes 1/32 of the validator’s stake immediately, ejects the validator from the set, and imposes a correlation penalty during the 36-day withdrawal delay period. If many validators are slashed simultaneously (suggesting a coordinated attack), the correlation penalty can reach 100% of stake — the entire deposit is burned.
Choosing the Right Consensus Mechanism
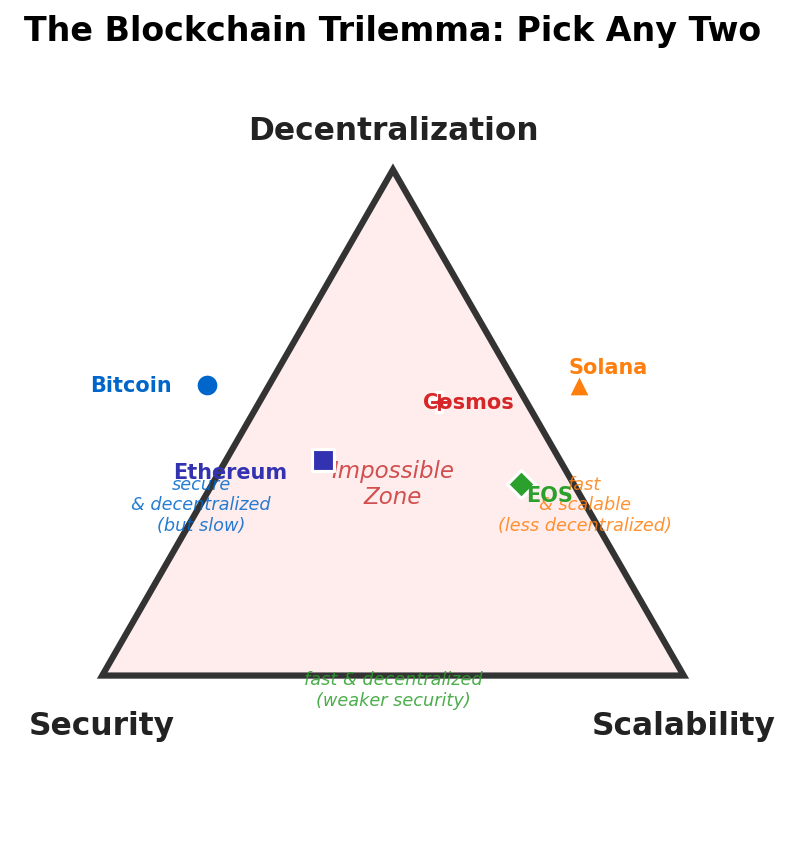
08Consensus mechanisms are not interchangeable defaults — they are fundamental architectural decisions with cascading consequences for security, decentralization, user experience, and economic structure. Choosing a mechanism requires mapping the system’s requirements onto the design space and accepting the trade-offs honestly.
1. How permissionless must participation be? Open to anyone with hardware/stake, or only known entities?
2. What finality latency is acceptable? Seconds (BFT), minutes (PoS), or hours (PoW confirmations)?
3. What is the security budget? How much capital or hashrate should an attack require?
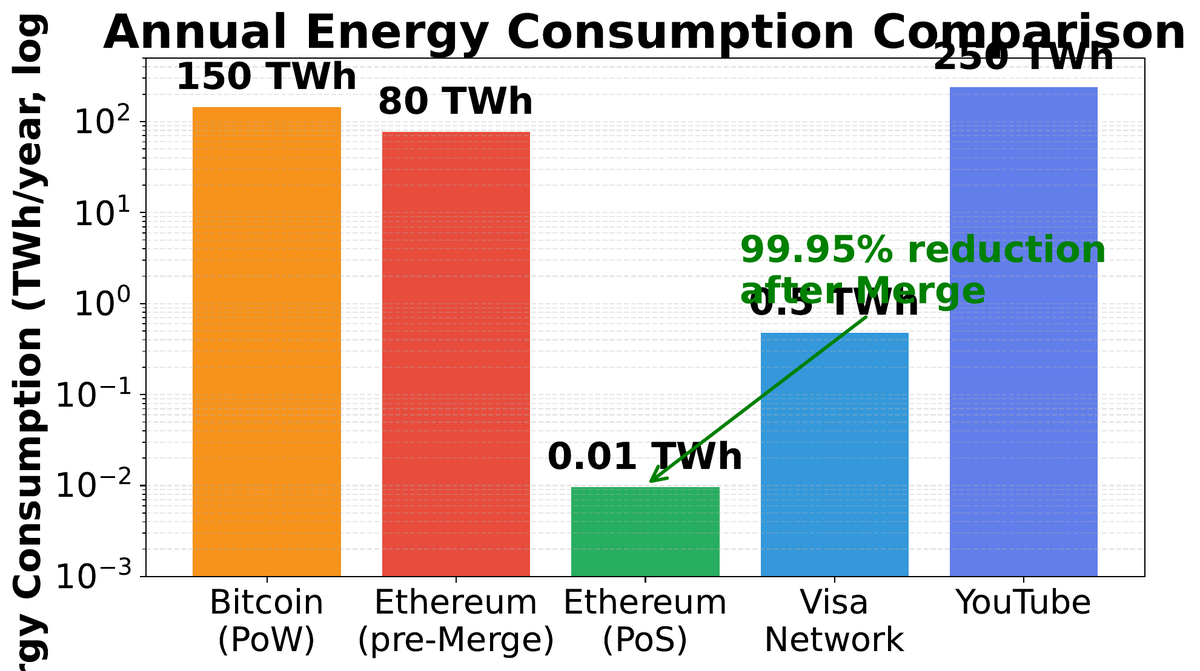
4. What is the energy and environmental constraint? Public institutions increasingly require PoS or PoA.
5. What happens under a liveness failure? Is it acceptable for the chain to halt, or must it continue at all costs?
Security
Cost to attack > expected gain. Measured by attack cost (PoW: hash rental; PoS: stake acquisition + slashing risk).
Decentralization
No small coalition controls consensus. Requires low barriers to validator entry and diverse, geographically distributed nodes.
Performance
High throughput and fast finality. Requires coordination overhead that conflicts with open participation and large validator sets.
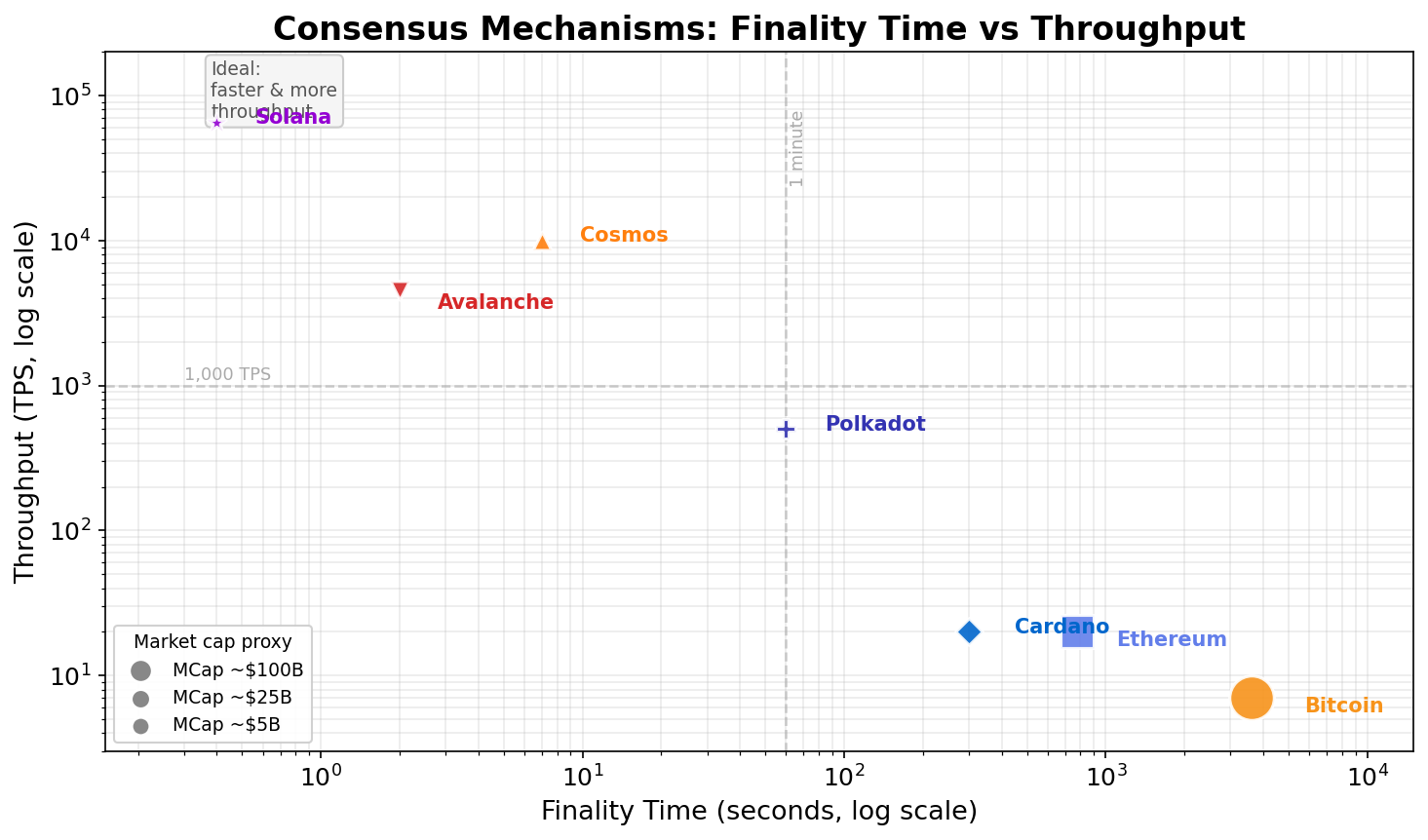
The trajectory of the field is clear: probabilistic PoW finality is increasingly confined to Bitcoin, where it is a deliberate ideological and security choice. New protocols overwhelmingly use PoS with BFT-style finality, accepting the requirement of a known or bonded validator set in exchange for fast finality and low energy consumption. The remaining open research question is whether strong decentralization (tens of thousands of validators) can coexist with BFT-style fast finality — Ethereum’s Danksharding roadmap and distributed validator technology (DVT) represent the current frontier of this challenge.
No consensus mechanism is universally optimal. Bitcoin’s PoW is the right choice for a global censorship-resistant monetary system where security must be provable without trust in any institution. Tendermint is the right choice for an application-specific chain within the Cosmos ecosystem where instant finality enables real-time UX and validators are economically accountable through governance. DPoS is the right choice if raw throughput is the priority and the community accepts the centralization trade-off. The engineer’s task is to match the mechanism to the threat model — not to find the one true consensus algorithm.