L13: The DAO Fork
The DAO Fork: A Story in Four Acts
01The DAO hack of June 2016 is the most studied crisis in blockchain history. It was the moment the Ethereum community was forced to answer a question nobody had prepared for: when a smart contract executes exactly as written but produces a catastrophic outcome, who has the authority to reverse it?
This lecture follows the story across four acts. Act 1: The Dream — an ambitious experiment in decentralised governance that attracted $150 million in weeks. Act 2: The Crisis — a reentrancy attack that drained 3.6 million ETH in hours. Act 3: The Dilemma — a community torn between two irreconcilable philosophies. Act 4: The Legacy — a chain split that produced two living blockchains and transformed smart contract security forever.
April 2016: A Radical Experiment Begins
02Ethereum is 10 months old. A team from Slock.it, led by Christoph Jentzsch, launches “The DAO” — a smart contract acting as a decentralised autonomous organisation modelled as a venture capital fund with no CEO, no board, and no headquarters. Just code and token holders voting on how to deploy funds.
Three properties made The DAO unprecedented:
The underlying thesis: replace institutional trust (lawyers, boards, regulators) with mathematical trust (cryptography, consensus, immutable code). It was the boldest test of the Ethereum vision to date.
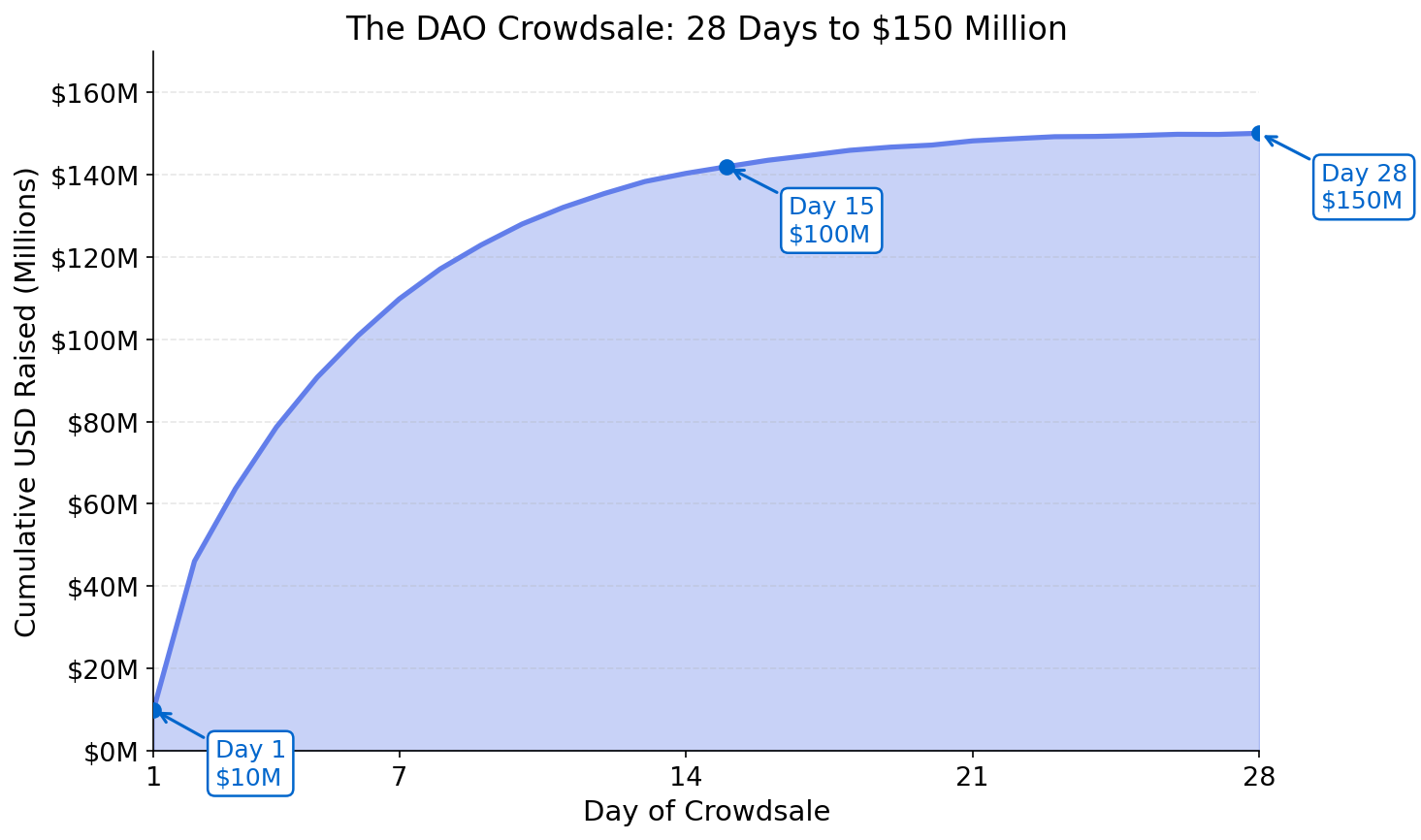
28 Days, $150 Million, 11,000 Investors
03The largest crowdfund in history (at that time). In 28 days, The DAO raised the equivalent of $150 million in ETH from approximately 11,000 individual investors worldwide — no intermediary, no underwriter, no minimum investment threshold.
| Metric | Value |
|---|---|
| Duration | 28 days |
| Total raised | ~$150 million |
| ETH locked | 3.6M ETH (14% of all ETH) |
| Investors | ~11,000 |
| Token rate | 1 ETH = 100 DAO tokens |
| Legal entity | None |
| Terms of service | None |
The Machine: How The DAO Made Decisions
04The DAO’s governance model had four stages: Propose → Debate → Vote → Execute. Any token holder could propose allocating funds to a project. The community debated it. Token holders voted (weighted by holdings). If the proposal passed, the smart contract disbursed the ETH automatically — no human intermediary required.
But there was a fifth function that would prove critical: splitDAO() — the exit door. If a token holder disagreed with the majority, they could call this function to leave The DAO and take their proportional share of ETH into a new “child DAO”.
The child DAO mechanism had one critical property: once you initiated a split and created a child DAO, there was a 28-day waiting period before the ETH could be withdrawn. This was a theft-prevention delay. It was also the feature that gave the community time to respond to the attack.
| Governance Function | Role | Risk |
|---|---|---|
| propose() | Submit a funding request | Low |
| vote() | Cast weighted vote on a proposal | Low (voter apathy) |
| executeProposal() | Disburse ETH to approved project | Medium (requires correct logic) |
| splitDAO() | Exit and create child DAO | CRITICAL — reentrancy vulnerability |
June 9, 2016: A Warning Nobody Heeded
05Security researcher Peter Vessenes publicly disclosed a reentrancy vulnerability in the splitDAO() function on June 9, 2016. The community read the report. The core developers acknowledged the concern. But the contract was already deployed on Ethereum.
Proposals were floated: could the community coordinate a “white hat” drain of the contract funds to a safe address before an attacker could exploit the bug? Could a soft fork freeze the vulnerable functions? Each plan required broad community coordination that could not be achieved in time.
Eight days passed. The warning was acknowledged. Nothing was fixed. On June 17, the attacker acted.
June 17, 2016: 3.6 Million ETH Vanishes
06The reentrancy attack exploited a race condition between the ETH transfer and the balance update in splitDAO(). The mechanism is often explained as the ATM analogy:
The technical root cause: the contract sent ETH before updating the sender’s internal balance record. The attacker’s malicious contract intercepted the ETH transfer via a fallback function, immediately re-called splitDAO(), and repeated the cycle dozens of times.
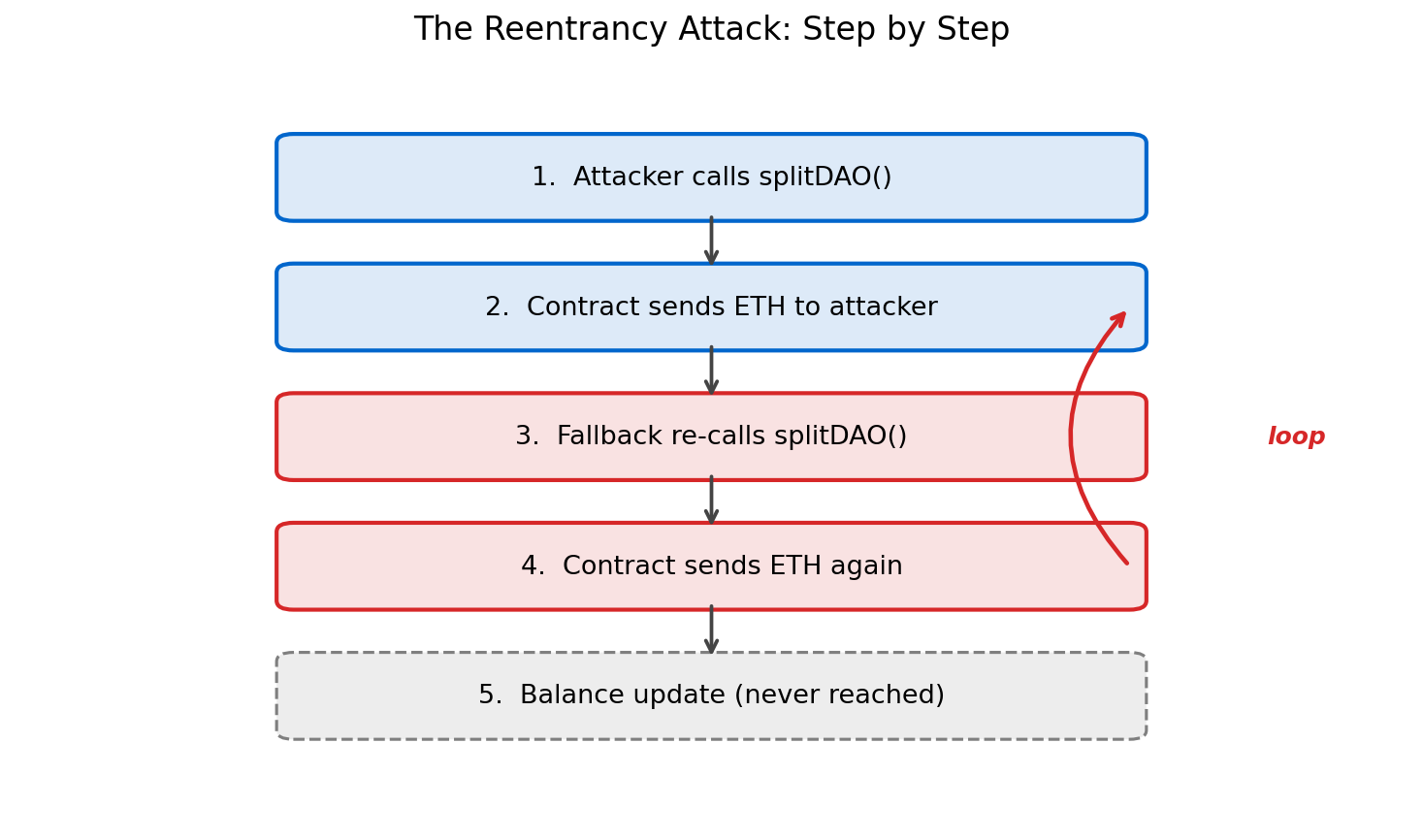
| Attack Detail | Value |
|---|---|
| Date | June 17, 2016 |
| ETH drained | 3.6 million ETH (~$60 million at the time) |
| Percentage of DAO funds | ~30% of total holdings |
| Lock period remaining | 28 days |
| Fix | Checks-Effects-Interactions pattern (always update state before sending) |
Panic, Proposals, and a Ticking Clock
07The community response compressed weeks of deliberation into days. ETH price dropped 33% within hours of the attack being discovered. Exchanges halted DAO token trading.
- June 17Attack discovered. Ethereum community enters crisis mode. ETH drops from ~$20 to ~$13.
- June 18Vitalik Buterin proposes a soft fork: modify the Ethereum protocol to freeze any transactions moving the stolen ETH. Miners would implement by updating software.
- June 21The attacker publishes an open letter arguing the funds were legally obtained under the DAO’s own rules: “I followed the code’s rules. This is not theft.”
- June 24Security researchers discover the soft fork proposal itself has a Denial-of-Service vulnerability — it could be used to spam the network with free transactions. The soft fork is abandoned.
- June 28The only remaining option: a hard fork that manually moves the stolen ETH to a refund contract, reversing the attack at the protocol level.
- July 15Community vote closes. Hard fork proceeds to implementation.
- July 20Hard fork executes at block 1,920,000. Ethereum splits.
Code Is Law vs. The Will of the People
08The hard fork debate exposed a philosophical fault line that had always existed in blockchain culture but had never been tested at scale. The question was not technical. It was political: who has ultimate authority over a blockchain?
Against the Fork: “Code Is Law”
The contract executed exactly as written. No rule was broken — only a design flaw exploited within the defined rules. Reversing the transaction destroys Ethereum’s core guarantee: immutability. If developers can undo transactions once, they can undo them again whenever powerful people lose money. The fork sets a precedent that Ethereum’s ledger is not censorship-resistant — it is subject to developer veto. Ethereum Classic maintains that this principle, once broken, cannot be restored.For the Fork: “Intent Matters”
The attacker exploited a bug, not a feature. The difference between intent and outcome matters morally, even if the code made no such distinction. A nascent ecosystem cannot survive a $60M theft in its first year — it would destroy the credibility of Ethereum as a platform for serious applications. Ethereum is a social contract, not just software. Communities have always exercised governance over shared infrastructure. The code’s immutability is a technical property, not a moral command.Neither side was wrong. Both were asking legitimately different questions. The “code is law” camp prioritised systemic trust over individual outcomes. The “intent matters” camp prioritised ecosystem viability over philosophical purity. The debate reflects the deeper tension between algorithmic governance and human governance that every blockchain community eventually confronts.
The Community Decides: Fork or No Fork?
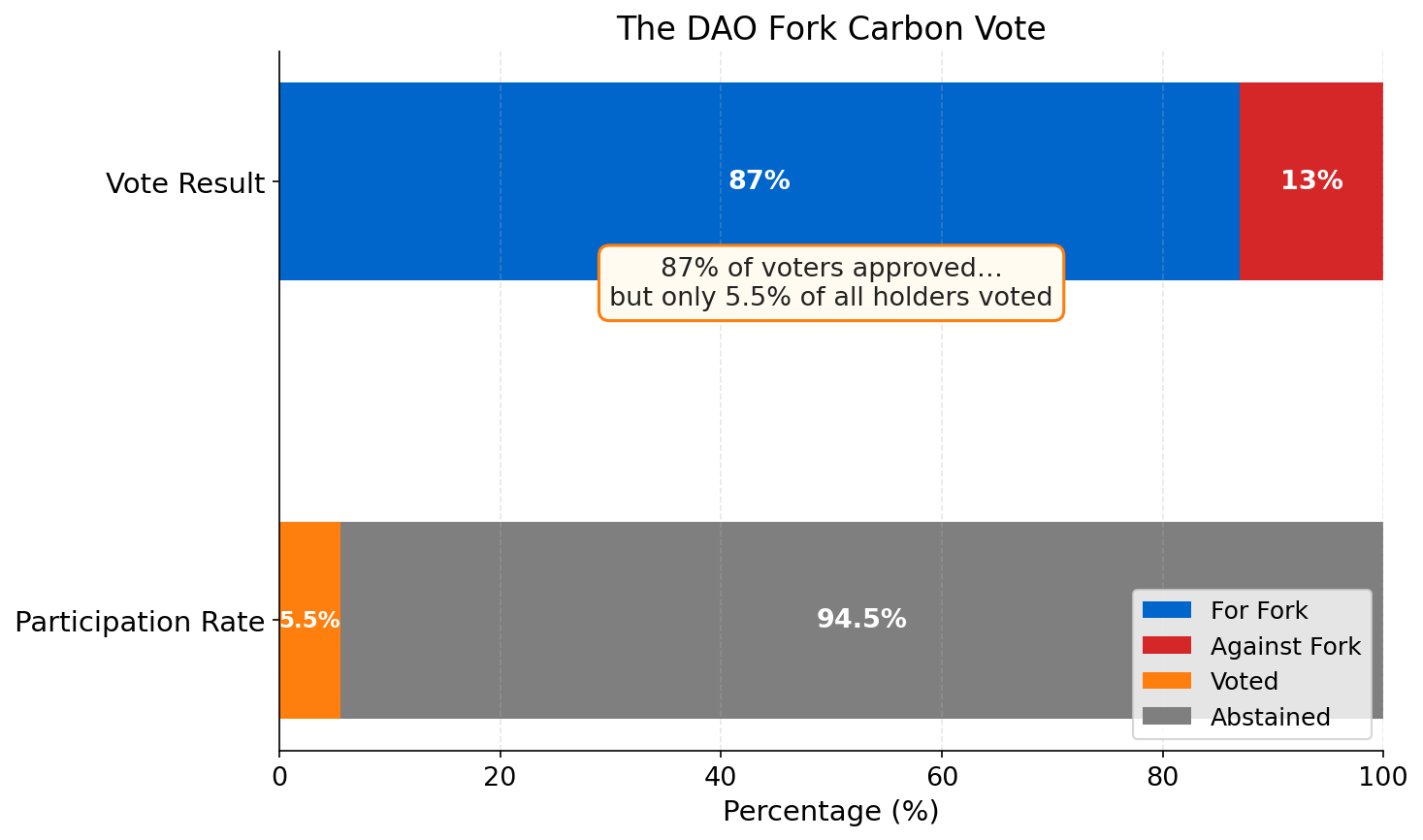
09The Ethereum Foundation organised the Carbon Vote, an on-chain governance experiment where ETH holders could signal their preference by sending a transaction. The results were decisive — but raised immediate questions about legitimacy.
| Vote Outcome | Result |
|---|---|
| For the hard fork | 87% of voting ETH |
| Against the fork | 13% of voting ETH |
| Voter turnout | ~5.5% of all ETH |
| Large holder bias | Yes — whale-weighted |
The Carbon Vote is often cited as evidence both for and against on-chain governance. It showed that coordination was possible at speed. It also showed that plutocratic weighting and low participation are structural risks in token-weighted voting.
Block 1,920,000: Ethereum Splits in Two
10On July 20, 2016, at block 1,920,000, the Ethereum Foundation deployed an irregular state transition — a one-time, manually authored change to the blockchain state outside of the normal transaction rules. The stolen ETH was moved to a refund contract. Investors could retrieve their ETH.
But not all miners ran the new software. A minority of miners continued to build on the original, unforked chain — the one where the attacker’s funds remained intact. The two chains shared identical history up to block 1,919,999. From block 1,920,000 onwards, they diverged permanently.
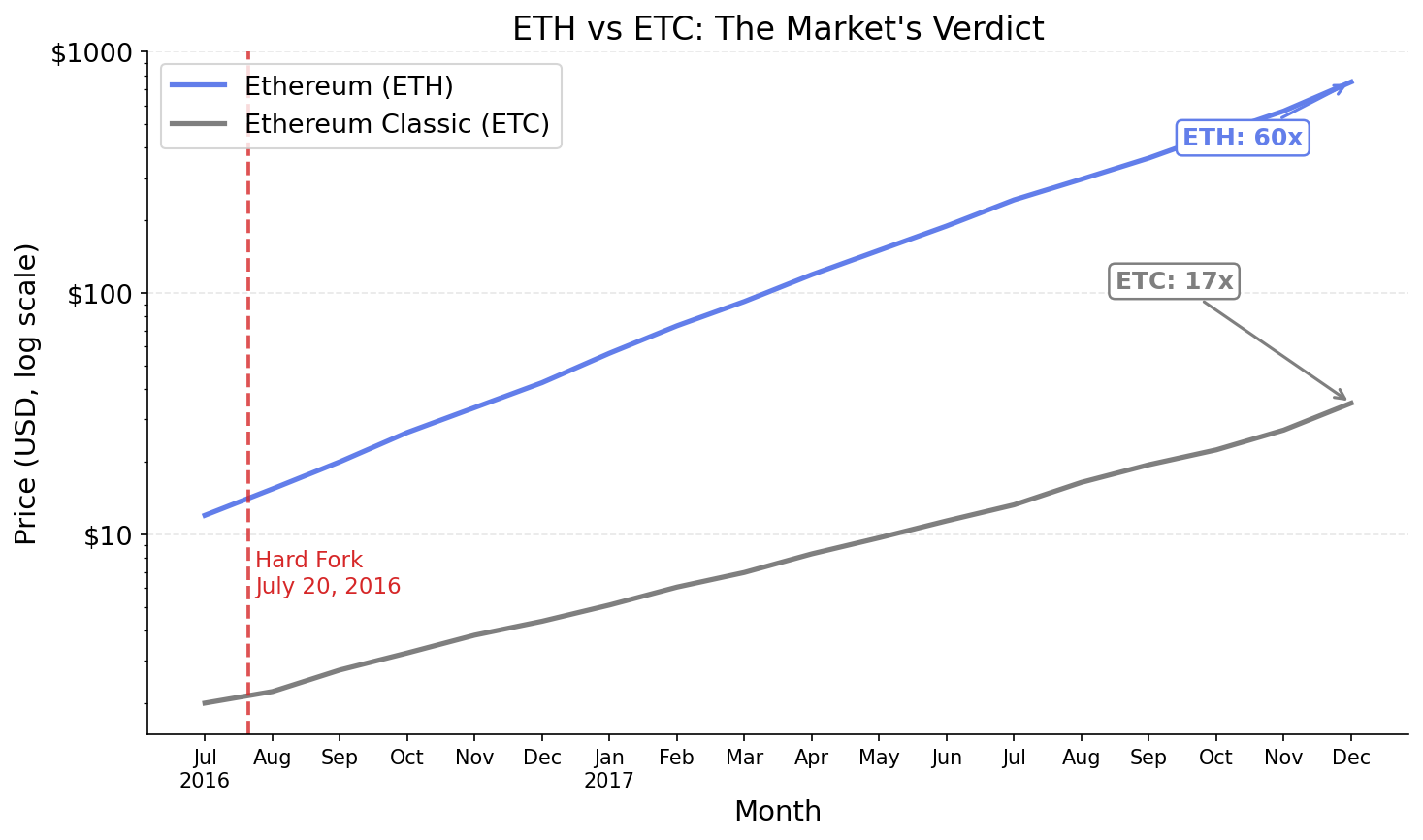
The market spontaneously assigned names and ticker symbols. The forked chain — with the refund — became Ethereum (ETH). The original chain — where the attacker’s funds remained — became Ethereum Classic (ETC).
| Property | Ethereum (ETH) | Ethereum Classic (ETC) |
|---|---|---|
| Fork applied | Yes — funds refunded | No — original state |
| Philosophy | Intent matters; community governs | Code is law; immutability absolute |
| Development team | Ethereum Foundation | Separate community |
| Market outcome | Dominant; grew to #2 by cap | Survived; 51%-attacked in 2020 |
Two Chains, Two Philosophies, Two Prices
11The market rendered its verdict with price. ETH recovered, grew, and became the foundation of DeFi, NFTs, and the smart contract economy. ETC survived but never achieved comparable adoption, and its smaller hashrate left it vulnerable to 51% attacks.
Lessons That Apply to Every Blockchain Project
12The DAO crisis produced five lessons that have shaped blockchain development and governance ever since. Each directly contradicted assumptions that the 2016 community held.
- Smart contracts are immutable — test before you deploy. There is no patch, no hotfix, no support ticket once code is live on a public blockchain. The cost of a bug in production is borne entirely by users. Comprehensive testing, fuzzing, and formal verification are not optional extras — they are the minimum viable security posture for any contract holding significant value.
- “Code is law” has limits. Communities will intervene when the stakes are high enough. The DAO fork proved that no amount of philosophical commitment to immutability will survive a $60 million crisis with a 28-day window. Every blockchain is ultimately a social consensus machine. The code is the mechanism; the community is the authority.
- Governance is the hardest problem. Technical consensus (miners, nodes running the same software) is achievable by protocol design. Social consensus (developers, users, investors, exchanges, regulators) is not. The DAO fork required both simultaneously — and nearly failed at the social layer despite broad technical agreement.
- Security audits are not a checkbox. The DAO was audited. But the audit was incomplete and rushed. A thorough security audit is a process, not a timestamp. It requires time, adversarial thinking, and the willingness to delay deployment when findings are unresolved.
- Forks are the ultimate governance mechanism. When a community cannot reach consensus, it splits. Both outcomes can coexist. Markets and developers determine which vision survives. This is not a bug in decentralised systems — it is a feature. Dissenting minorities can exit with their assets rather than being permanently outvoted.