L01: Introduction to Blockchain
The Problem: Trust Without Intermediaries
01Every digital payment system before Bitcoin shared one structural weakness: a trusted third party sat at the center. Banks, clearinghouses, and payment processors are not just conveniences — they are architectural requirements. Alice cannot simply send Bob a digital file labelled “$10” because Bob has no way to verify that Alice has not sent the same file to a hundred other people simultaneously. This is the double-spend problem, and solving it without a central authority was considered an open problem in distributed systems for decades.
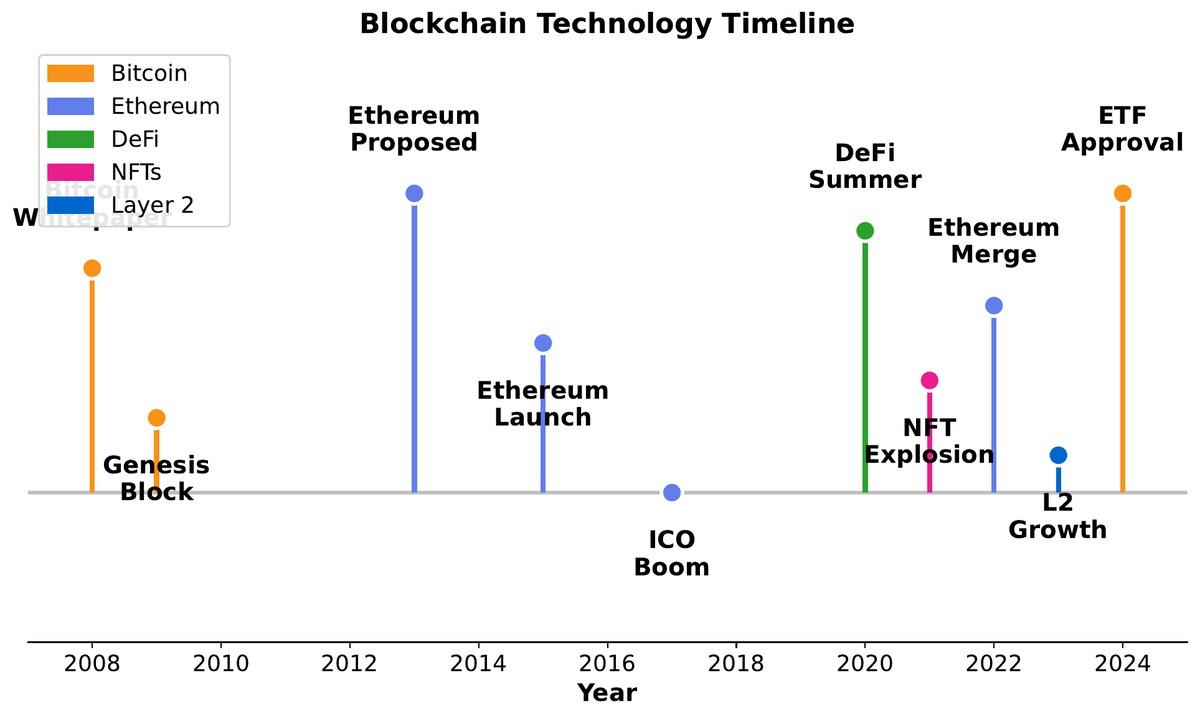
The 2008 financial crisis sharpened the critique. When Lehman Brothers collapsed and governments bailed out the institutions that had failed ordinary depositors, a cypherpunk community asked an uncomfortable question: what would a monetary system look like if trust in institutions were optional rather than mandatory? Satoshi Nakamoto’s answer, published in October 2008, was to replace institutional trust with cryptographic and game-theoretic guarantees enforced by a globally distributed network.
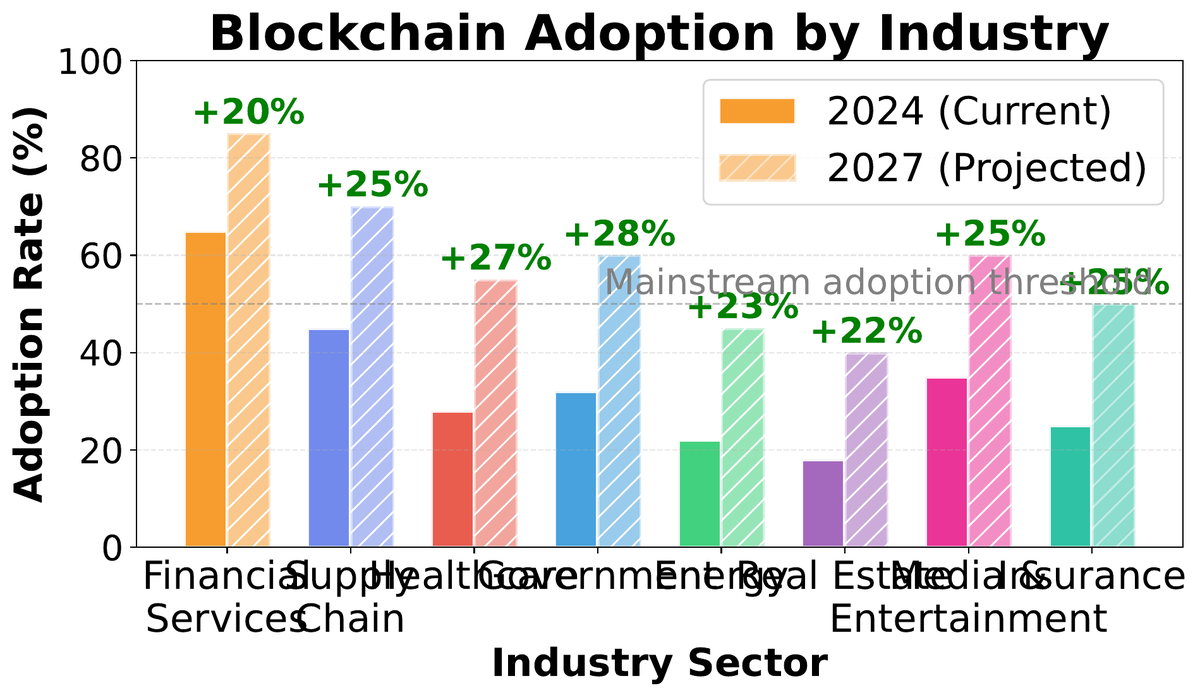
Beyond payments, the same trust problem appears in supply chains (who vouches that this diamond was not conflict-sourced?), voting systems (who certifies the count was not altered?), and intellectual property (who timestamps the moment of creation?). Blockchain’s core proposition is a tamper-evident, append-only ledger maintained by parties who do not necessarily trust each other — a “truth machine” that is expensive to corrupt because corruption requires outspending all honest participants combined.
Foundations: Definition, Anatomy, and the Trilemma
02A blockchain is a distributed, append-only data structure in which records (transactions) are grouped into blocks, each block containing a cryptographic hash of its predecessor. This hash linkage means that altering any historical block invalidates every block that follows — making retrospective fraud computationally visible to the entire network.
Each block consists of three logical layers. The header stores metadata: the previous block’s hash, a timestamp, the difficulty target, and the nonce used to satisfy the proof-of-work puzzle. The Merkle root is a single 32-byte fingerprint that summarises every transaction in the block — changing even one byte anywhere in the transaction set changes the root. The body contains the ordered list of transactions themselves.
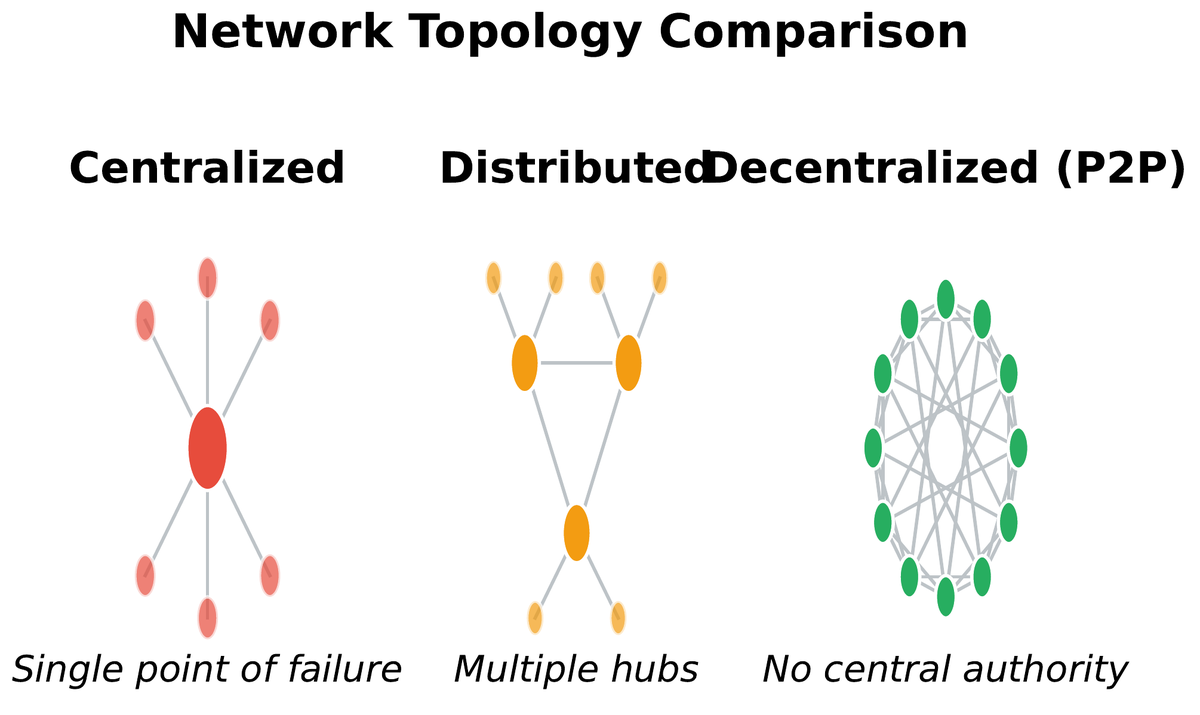
The choice of blockchain architecture involves navigating the Blockchain Trilemma (Buterin, 2017): any system can achieve at most two of three properties simultaneously. Security ensures that the canonical chain cannot be rewritten cheaply. Decentralization ensures that no small coalition controls consensus. Scalability ensures the system can process transactions at a rate matching real-world demand.
Security
Resistance to Sybil attacks, 51% attacks, and history revision. Achieved via PoW cost or PoS slashing.
Decentralization
No single entity controls block production or validation. Requires many independent nodes.
Scalability
High transaction throughput (thousands of TPS). Requires coordination overhead that conflicts with full decentralization.
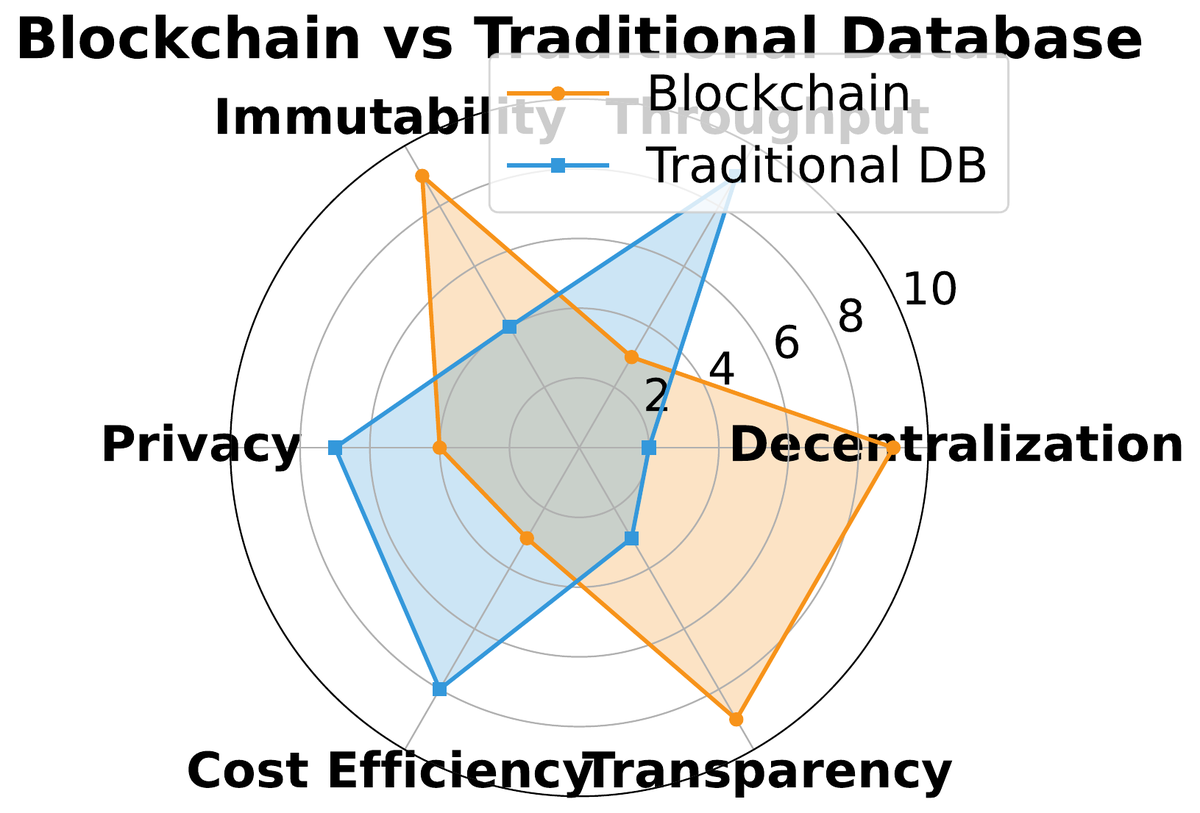
| Property | Traditional DB | Permissioned Chain | Public PoW Chain | Public PoS Chain |
|---|---|---|---|---|
| Write access | Authorized only | Consortium members | Anyone (by mining) | Anyone (by staking) |
| Read access | Controlled | Members | Public | Public |
| Immutability | Low | Moderate | High | High |
| Throughput (TPS) | >10,000 | 1,000–10,000 | 3–7 | 15–100,000 |
| Energy use | Low | Low | Very high | Low |
| Trust model | Central admin | Consortium | Algorithmic | Algorithmic |
How It Works: Hash Chaining, Transactions, Consensus
03The fundamental mechanism is elegantly simple: each block commits to the entire history before it through a single hash. If a malicious actor wants to alter block 500, they must recompute block 500’s proof-of-work, then block 501’s, then 502’s, and so on all the way to the chain tip — all while the honest network continues extending the chain. The attacker must permanently outpace every honest miner combined. On the Bitcoin network, that currently requires over 500 exahashes per second of sustained computation.
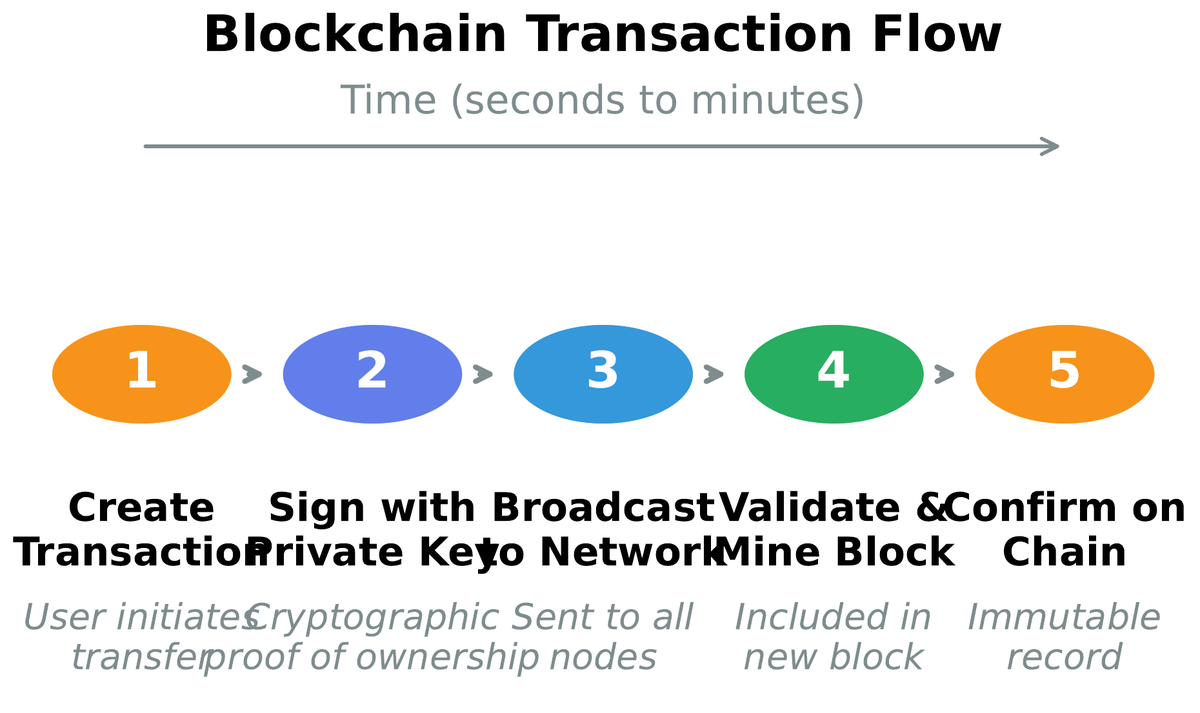
A Bitcoin transaction is not a simple file transfer. It is a script that destroys existing unspent transaction outputs (UTXOs) and creates new ones locked to recipient addresses. The sender proves ownership by producing a valid digital signature with the private key corresponding to the locked address. This UTXO model means the blockchain never stores balances directly — a wallet balance is the sum of all UTXOs locked to the user’s addresses, computed on-the-fly.
Proof-of-Work (PoW) is the original Nakamoto consensus mechanism. Miners repeatedly hash a block header with incrementing nonce values until the result falls below a target threshold — a lottery where buying more tickets (hash power) increases your probability of winning. The difficulty adjusts every 2016 blocks (roughly two weeks) to keep average block time at 10 minutes regardless of total hash rate. This self-adjusting difficulty is one of Bitcoin’s most elegant engineering decisions.
Mechanisms: Throughput, Smart Contracts, Economics
04Bitcoin’s 7 TPS ceiling is not a bug — it is a deliberate design trade-off. Larger blocks propagate more slowly across the network, giving well-connected miners a latency advantage and nudging the system toward centralization. Ethereum made different trade-offs, settling at ~15 TPS at launch, with the post-Merge PoS upgrade and the Layer 2 ecosystem pushing effective throughput far higher. Understanding these numbers requires distinguishing base layer TPS from effective TPS when rollups are included.
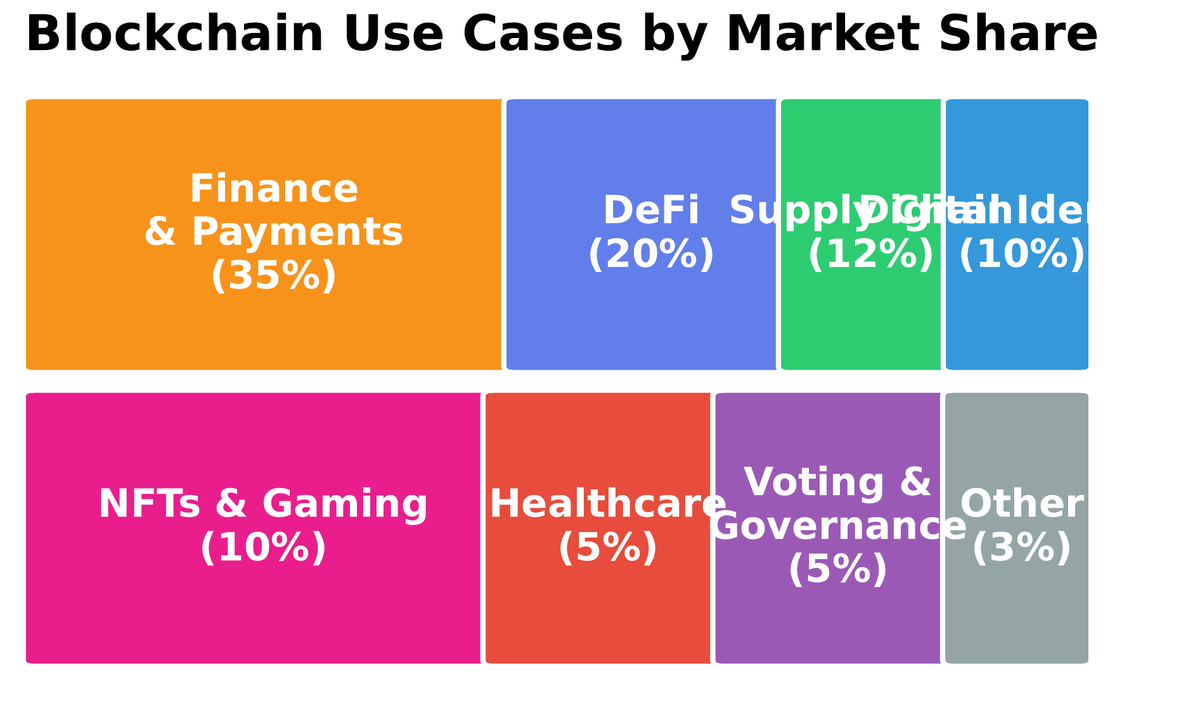
Smart contracts extend the ledger from passive record-keeping to active computation. Introduced by Nick Szabo in 1994 and first implemented at scale on Ethereum in 2015, smart contracts are programs stored on-chain whose execution is triggered by transactions. Because every full node executes the same code against the same state, the outcome is deterministic and cannot be altered by any single party after deployment. This enables trustless escrow, decentralised exchanges, lending protocols, and DAOs without a central operator.
Mining economics shape long-run network security. A rational miner compares block reward (subsidy + fees) against marginal cost of electricity and hardware amortization. As Bitcoin’s block subsidy halves every 210,000 blocks (~4 years), the fee market must grow to compensate — a transition whose economic sustainability remains an open research question. Ethereum’s EIP-1559 introduced a base-fee burn mechanism that ties ETH issuance directly to network demand, creating a deflationary pressure absent from Bitcoin’s design.
Challenges: Attacks, Failures, and Structural Limits
05A 51% attack occurs when a single entity controls the majority of a Proof-of-Work network’s hash rate. The attacker can privately mine a fork, eventually releasing it to replace the public chain — reversing transactions and double-spending. Bitcoin has never suffered a successful 51% attack because the cost of acquiring and operating >50% of its hash rate exceeds expected profit. Smaller PoW chains are substantially more vulnerable: Ethereum Classic, Bitcoin Gold, and Vertcoin have all experienced confirmed 51% attacks.
Smart contract vulnerabilities are structurally different from traditional software bugs because deployed code is immutable. A flawed banking app can be patched overnight; a flawed smart contract holding $1 billion in assets cannot be changed without a coordinated governance decision. Reentrancy attacks, integer overflow, oracle manipulation, and flash loan exploits have collectively cost DeFi users billions of dollars. Formal verification, audit practices, and upgradeable proxy patterns are partial mitigations, each with their own trust trade-offs.
The three structural challenges that no current chain has fully solved are scalability (processing thousands of TPS at layer 1 without sacrificing decentralization), energy consumption (PoW mining consumes electricity comparable to mid-sized countries), and regulatory uncertainty (securities classification, AML/KYC requirements, and cross-border enforcement remain unsettled in most jurisdictions). These are not merely engineering problems — they involve political economy, law, and coordination at a global scale.
Evidence: Markets, Regulation, and Adoption
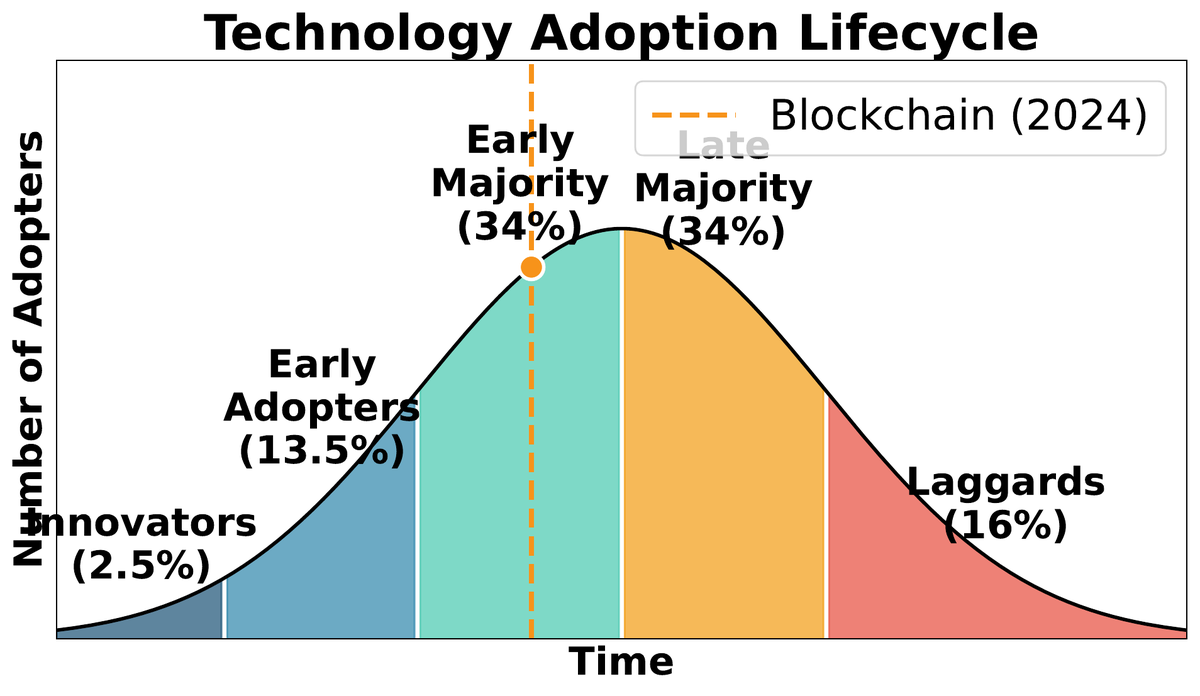
06Blockchain has moved from cypherpunk experiment to regulated asset class in under fifteen years. Bitcoin’s market capitalization peaked at approximately $1.3 trillion in late 2021 and the total crypto market exceeded $3 trillion. Spot Bitcoin ETFs were approved in the United States in January 2024, opening the asset class to institutional investors with fiduciary constraints. Ethereum’s transition to Proof-of-Stake in September 2022 reduced its energy consumption by over 99.9%, removing the most prominent environmental objection.
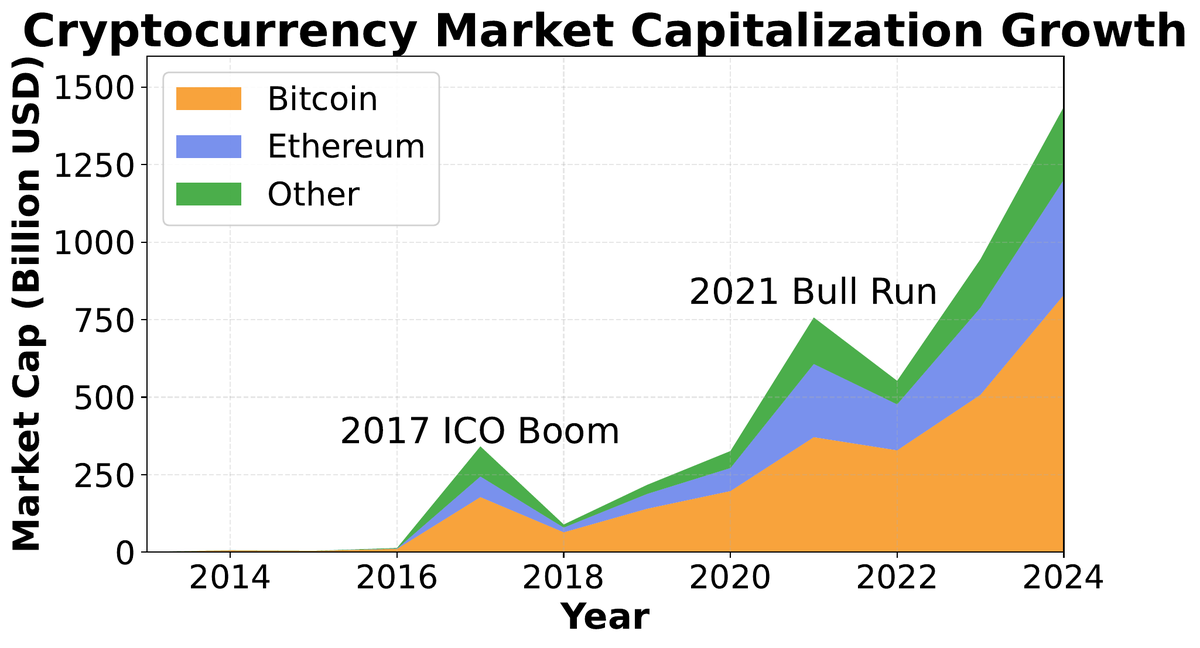
Regulatory responses have diverged sharply by jurisdiction. The EU’s MiCA regulation (Markets in Crypto-Assets, 2023) established the world’s first comprehensive crypto regulatory framework, covering stablecoins, exchanges, and issuers. The United States has proceeded via enforcement action rather than legislation, with the SEC bringing major cases against exchanges and token issuers. China banned crypto trading and mining entirely in 2021. This regulatory fragmentation creates compliance complexity for global operators and may shape where the next wave of blockchain innovation concentrates.
Stakeholders: Who Wins, Who Loses
07Disruption is not symmetric. Blockchain creates clear winners and losers across the financial and information economy. Understanding these distributional effects is essential for evaluating whether a blockchain application creates genuine value or merely redistributes it — or worse, concentrates it among early adopters at the expense of latecomers.
• Unbanked populations (1.4B globally) gaining access to financial services
• Creators capturing more value through NFT royalty mechanisms
• Developers building permissionless applications without gatekeepers
• Users in high-inflation economies using stablecoins as store of value
• Cross-border migrant workers paying <1% remittance fees vs. 6-8%
• Payment processors and clearinghouses (disintermediated)
• Traditional custodians and prime brokers
• Notaries and title registry services
• Retail investors in speculative tokens (asymmetric information)
• Miners in a PoW-to-PoS transition (stranded capital)
The generation gap is pronounced. Blockchain-native institutions (Coinbase, Uniswap, MakerDAO) were built from the ground up for a world of programmable money and open protocols. Traditional financial institutions face a dilemma: adopting blockchain technology means accepting open, auditable systems that may reduce the opacity on which some revenue models depend. Early corporate blockchain experiments (Ripple for cross-border payments, JP Morgan’s JPM Coin, trade finance consortia) suggest incumbents will adopt private or permissioned chains rather than public ones — preserving control at the cost of the core trustless property.
Evaluation: Five Questions and the Trust Spectrum
08After covering the mechanics, a rigorous engineer asks: should this be a blockchain? Most proposed applications do not survive contact with five diagnostic questions. Answering them honestly separates genuine use cases from motivated reasoning dressed in technical vocabulary.
1. Is shared write access genuinely needed? If only one party writes, a database is simpler.
2. Do the writers distrust each other? If trust exists, a shared database with an audit log suffices.
3. Can a trusted third party be avoided? If a TTP is acceptable, the blockchain’s cost may not be justified.
4. Are the rules static or do they need to adapt? Immutability is a feature only if governance is stable.
5. Is public verifiability valuable enough to justify transparency costs? Confidential business data is difficult to put on a public chain.
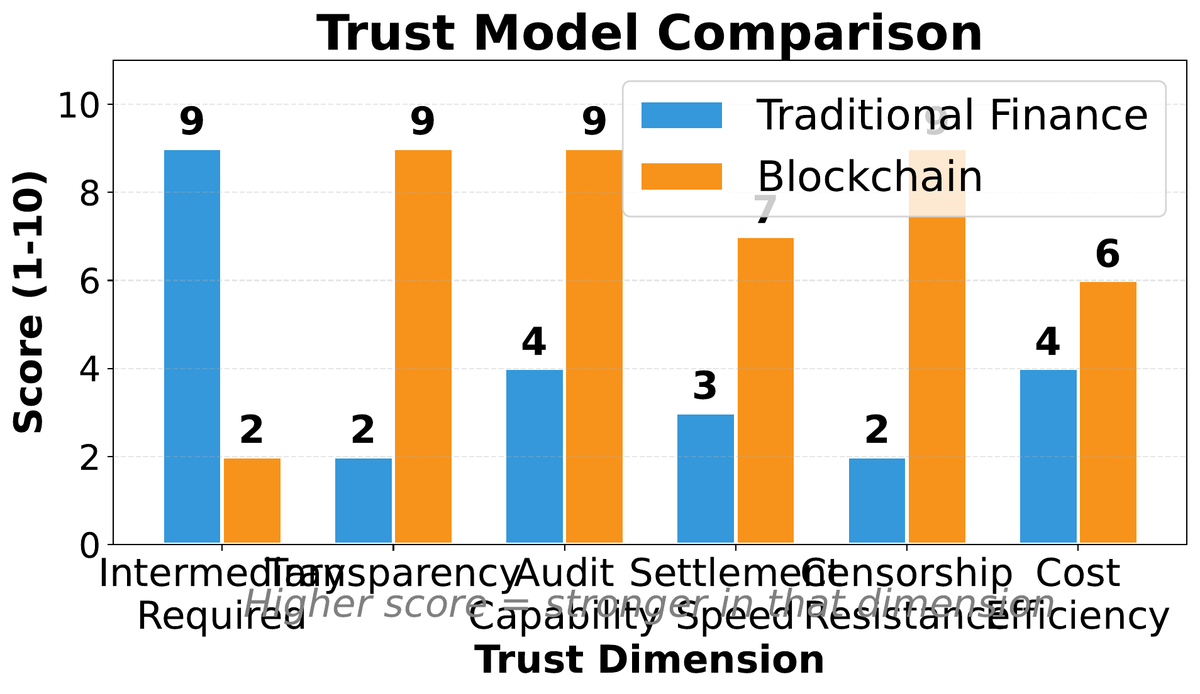
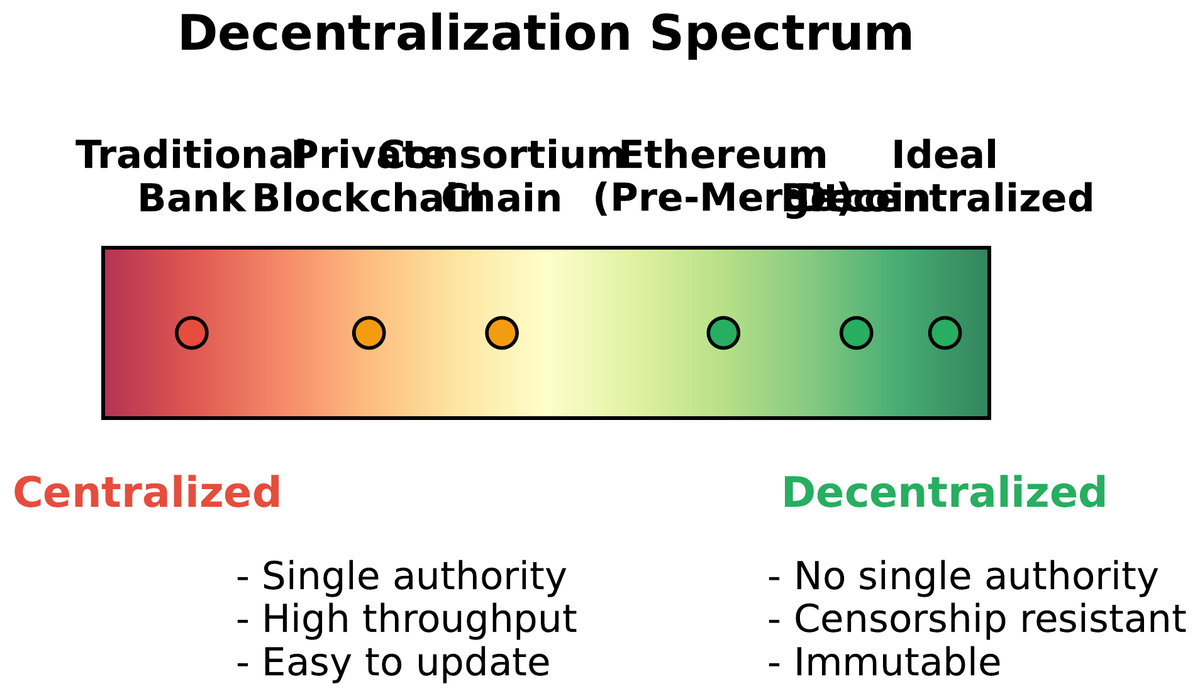
The trust spectrum runs from fully trusted (a bank’s internal ledger) through consortium trust (Hyperledger Fabric among supply chain partners) to trustless (Bitcoin, Ethereum). Moving right on the spectrum increases auditability and censorship-resistance but reduces performance and privacy. The appropriate point on the spectrum depends on the application’s threat model and the value placed on decentralization as a property in itself.
Blockchain technology is neither a universal solvent nor a solution in search of a problem — it is a specific tool with specific trade-offs. The engineer’s task is to match the tool to the problem. This course will give you the technical depth to make that judgment for the full range of blockchain architectures, from Bitcoin’s austere UTXO model to Ethereum’s Turing-complete EVM to the emerging Layer 2 landscape. The same analytical framework you apply here will serve you in every subsequent lecture.